Torzon Market showed up on the dark web in September 2022, and it’s been growing steadily ever since. These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services. It also runs on the Tor network, which helps keep things anonymous. Everything is in English, but users from around the world are welcome.
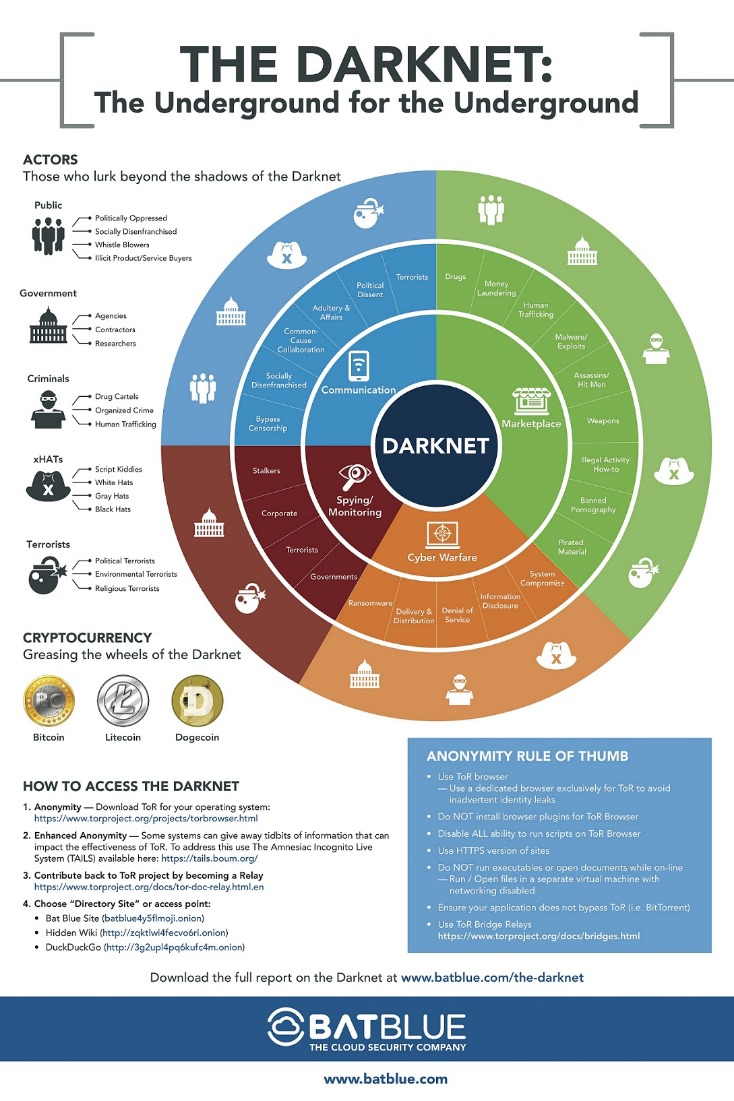
- Individuals began using the darknet to pseudonymously sell illegal content without face-to-face interaction.
- Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.
- You may also use it to access the regular internet more anonymously.
- If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
- Just visiting these sites can attract attention from law enforcement, especially if you interact with known vendors or download suspicious content.
One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser.
If your information has been compromised, then it’s likely that your phone number is also on the dark web. One of the great things about Tor is that it can be used to access both the dark and surface web. Just note that although you’ll be anonymous, you won’t have the speed or convenience of a direct connection, and some sites might block you outright. For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information.
Transactions are conducted through Bitcoin and Monero which provides anonymity for both buyers and sellers. Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption. Let’s get this straight — not everything on the dark web is illegal or harmful.
Key Cyber Threats Facing The Financial Sector In 2025

DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Open up Tor, and you won’t suddenly see the dark web staring back at you. Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs.
Navigating Dark Web Marketplace Links

These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data.
- The world of the darknet has always attracted the attention of the masses.
- The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more.
- In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone.
- In conclusion, the darknet continues to evolve, providing a secure and efficient platform for drug trade.
Features That Make WTN Market A Secure Platform
Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.
The Three Internets
The sad reality is the fact that law enforcement agencies can’t track and prosecute perpetrators or even take down such content given the anonymous nature of the dark web. As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums. Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts. The dark web is only accessible through specific software like Tor (The Onion Router).
Acronis Cyber Protect Cloud: New Version C2505
It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. In fact, everything is in English, and the site picks up users everywhere in the world. People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware. While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users. It’s a market for fake documents, hacking software, and financial fraud services. WeTheNorth has a strong community vibe, with an active forum where users interact and share updates.

Secure Messaging

As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.
How To Protect Your Identity While Browsing The Dark Web
As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact.

Meanwhile, cybersecurity experts monitor the dark web, scanning for stolen data and emerging threats. If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
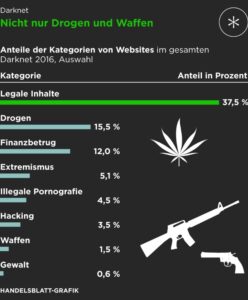
Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is. In many countries, strict laws limit who can legally buy, own, or carry firearms. Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. So, what even is this dark web, and why are these marketplaces present there?