The pages exist on standard servers, but their privacy controls prevent public indexing, keeping sensitive data out of search results. In an era defined by digital connectivity, protecting sensitive, critical and personal information from cyber threats – including those originating from the dark web – is a strategic imperative. Darknet Index offers a regularly updated list of verified and working links to active darknet markets, you can check out our updated 2025 top darknet market list with links. This is important because many market links often change due to various issues such as law enforcement actions or internal problems with the market itself which happens very rarely. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
Darknet Websites
Using a VPN is perhaps the easiest and most efficient way to protect your online travels from prying eyes, as it hides your real IP address, and encrypts all of your online traffic. Merely downloading, installing and using the Tor Browser is not illegal. However, some Tor users do so to facilitate illegal online acts.
Is It Illegal To Access The Dark Web?
Never install extensions or additional add-ons, even if they seem useful. They change your browser fingerprint and make you easier to track. It offers outstanding privacy features and is currently available at a discounted rate. This information can be used to target ads and monitor your internet usage.
Exodus Market – A Genesis Market Alternative
LifeLock notifies you if we find your personal information on the dark web, and we’ll help you run damage control with assistance from legal experts and recovery specialists. There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data. Learn more about the kinds of sites that can be found on the dark web and how you can access them.
As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact.
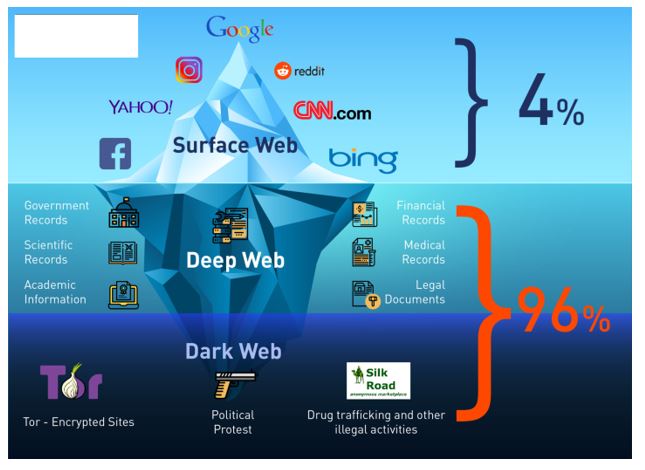
The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted. I2P is a private network built for secure, anonymous communication. Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation. It uses its own internal DNS to access “eepsites”, not .onion addresses. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web.
- Step into the world of Archetyp, where anonymity reigns supreme.
- The attacks have led to the formation of other cybercriminal groups and Cyber Extortion.
- It guides you through downloading and setting up all three browsers.
- That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web.
- While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance.
- Genesis Market and BidenCash, two top dark web marketplaces, were also shut down in 2023 and 2025, respectively.
Other Collection Links:
Your Internet service provider, or ISP, is your gateway to the Internet. While a website can’t identify you or an ISP can’t decrypt your internet traffic; still, they can still see you using Tor, which can draw some unwanted attention and raise suspicions. Many turn to the dark to grab such medications with its private and secure networks.
Disadvantages Of The Tor Browser

This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. Tor routes your traffic through a chain of relays to obscure your IP address. This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing.
We’ll focus on secure, ethical practices tailored to cybersecurity professionals and IT leaders. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers.
Security Links
The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. The users of the dark web are typically aiming to block governments from snooping on them.
What Do People Sell Or Exchange On Darknet Markets?
Think of it as the courier handing your unsealed letter to the recipient’s mailbox. Using HTTPS (the lock icon) or a VPN‑over‑Tor adds another envelope. Operation Cronos in February 2024 dismantled LockBit, seizing 11,000 dark‑web domains after the ransomware gang extorted more than $120 million. Yet threat actors regroup quickly, leveraging generative AI, ransomware‑as‑a‑service and cryptocurrency mixers.
Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences.
Is It Legal To Access The Dark Web?
Efforts to host and index hidden sites flourished with platforms like DuckDuckGo and Not Evil, facilitating users in their pursuit of anonymity. When using Tor for enhanced privacy and anonymity, it’s crucial to consider the security of your email communications. While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing. These services can potentially log your IP address or expose your information through various means, undermining the benefits Tor offers. As the digital environment evolves, so do the tactics employed by cybercriminals, law enforcement agencies, and privacy advocates.