The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. It allows you to search for images, maps, files, videos, social media posts, and more. ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Advancements In Search Engine Technology
One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. It will offer you an additional layer of encryption to access the deep parts of the internet.
Download Tor Browser
If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.
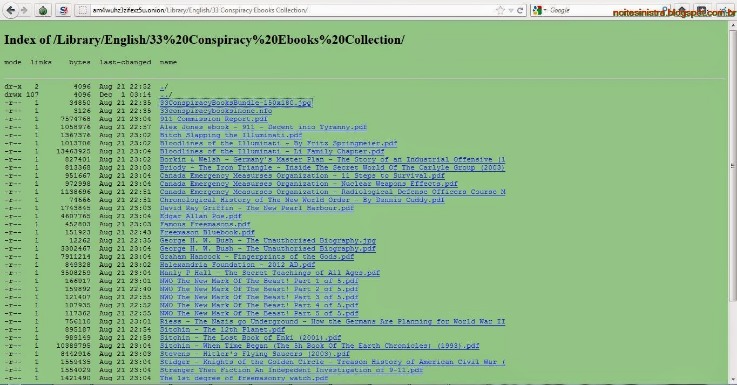
Deep Web Search Engine Links
The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Yes, you can access the dark web on mobile — you just need the right app. Android users need to download the Tor Browser app, while iPhone fans should get the Onion Browser app. Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust. ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy.
- We did not attempt to determine how many unique servers were underlying the domains we observed.
- Additionally, the deep web is increasingly being used for e-commerce.
- Many exit nodes are actually operated by law enforcement and scammers.
- But despite its many benefits, it’s sadly just a matter of fact that the dark web can be a dangerous place.
- Use specific keywords to refine your search results and avoid generic terms that may lead to irrelevant pages.
News, Media, And Other Information Organizations
So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. Services like Random Chat connects you with random people using the same service. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks
The dark web is often portrayed as vast and mysterious, implying that there is a large number of onion sites on Tor, but this is not what we find. This misperception may be in part due to the fact that there are many tragic and horrible things that take place under the anonymity Tor provides. Our crawling found 55,828 different onion domains, but only 8,416 were observed to be live on the Tor network during our crawl. Bitcoin mixers and “cleaning” services are showing signs of a continued rise in prevalence and sophistication.
Bobby Search
Dark markets use cryptocurrencies, such as Bitcoin, to facilitate transactions, adding an extra layer of anonymity. The darknet is a part of the internet that is not indexed by conventional search engines, often requiring specific software and configurations to access. It is a place where anonymity and privacy are highly valued, making it a frequent point of interest for researchers, privacy advocates, and individuals concerned about online security. The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security.
These .onion sites are hosted on the Tor network, which encrypts traffic and routes it through multiple nodes, making it extremely difficult to trace. This added layer of anonymity is what sets these links apart and is the reason so many seek out dark web links in the first place. Ahmia developers believe that the Tor network is an important distributed platform to protect anonymity and privacy around the world. Compared to these alternatives, our site stands out by offering more frequent updates, rigorous link verification, and a strict no-tracking policy that protects your privacy. We continuously monitor and remove malicious or outdated links faster than most directories, reducing the risk of scams. Additionally, we provide detailed descriptions and safety advice for each link, empowering users to make informed decisions.
Using a VPN is optional but highly recommended for users seeking maximum anonymity or those accessing sensitive content on the dark web. The Tor Browser looks and feels similar to a regular web browser but is configured to prioritize privacy and security by default. It blocks browser trackers and resists fingerprinting, which helps maintain your anonymity while browsing. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up.
Wikipedia manages one of the best Tor sites for encyclopedic knowledge. Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. Protect your business with end-to-end encryption and compliance-ready security.
Enter Your Email Address
The ratio of live to total onion domains was about 15% in our results. For each dark marketplace m that was shut down, we identify users who started trading on another coexisting marketplace \(m’\) after the closure of m. If a user was trading on both marketplaces m and \(m’\) before the closure of marketplace m, the user is not labelled as a migrant to marketplace \(m’\). In fact, migration was observed37 after the closure of the AlphaBay marketplace when other marketplaces, namely Hansa and Dream Market, experienced an abnormal spike in activity. Opening the onion links is very easy from the Tor browser, which you need to download and install in advance. To search for onion links for any website on the surface web, just copy-paste the URL in a Tor browser window.
These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name.
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. For this reason, you must watch out and avoid opening anything that looks suspicious to you. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities.
Some sites might use these details for advertising, analytics, or tracking your online preferences. This subreddit exists to debunk urban legends and share real verifiable information from the far reaches of the Tor dark web. Radar Rundown Ad blockers are the best protection against disruptive ads. While they might sound the same, these websites are fundamentally different. The wallet is free, and since it’s open-source, anyone can inspect, verify, and contribute to the code. Keybase is a dark web messaging application that functions much like Signal and WhatsApp, except it is secure and private.
Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law. With the above dangers, it’s imperative to tread carefully as you step into the dark web. Its source of funding is the deep wallet of the Sandler Foundation and various other similar organizations.