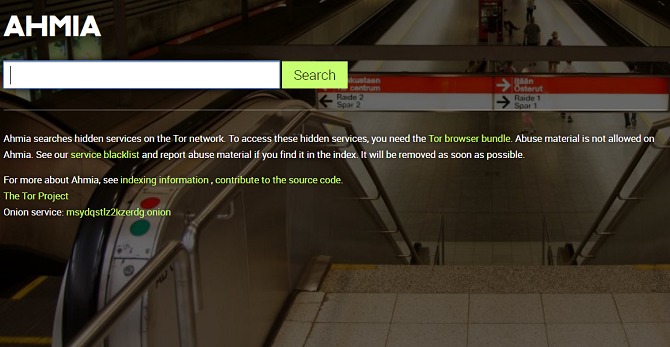
Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. I2P can only be used to access hidden sites that are only available on the I2P network. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. Then, simply click the operating system that you are using and download the file.
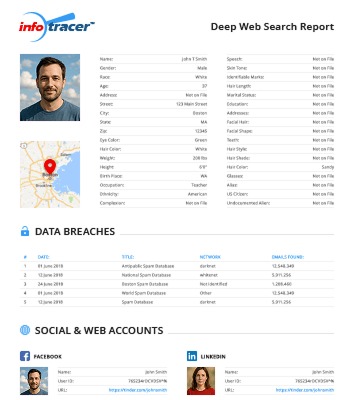
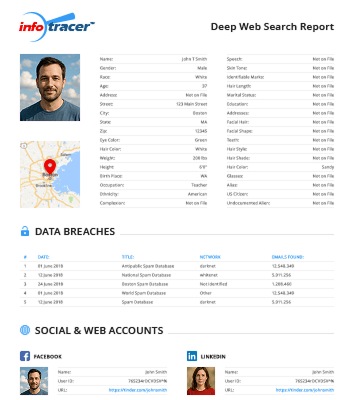
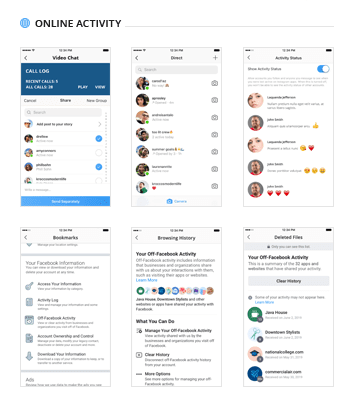
You can find out if someone keeps a secret social and dating profile or has any other hidden online activity. Another specialization is checking if your information has been leaked in a data breach by looking up leaked records. So, after running a search, there will be the location, email addresses, social media profiles, and even additional criminal records at your service. Due to thoughtful and continuously updated algorithms of search, it is easy to find the necessary goods, content, or information. Using Not Evil, you can save a lot of time and keep total anonymity. Similar work link Deep Web Search Engine, a Google Scholar allows you to search across a wide range of academic literature.
Since technology is not going anywhere and does more good than harm, adapting is the best course of action. We plan to cover the PreK-12 and Higher Education EdTech sectors and provide our readers with the latest news and opinion on the subject. From time to time, I will invite other voices to weigh in on important issues in EdTech. We hope to provide a well-rounded, multi-faceted look at the past, present, the future of EdTech in the US and internationally.
Cryptocurrency Services

There are several programs that hackers frequently use on the dark web. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Be warned that this may cause some websites to not work properly. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. Data gleaned from ransomware and data breaches is available on the dark web.
How To Safely Access And Use Deep Web Search Engines

The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins. It’s undoubtedly one of the best sites to download ebooks for free. Veridian Software is the company behind the now-dead portal for historical newspapers, Elephind. If you loved Elephind and want an alternative, you’ll be happy to know that all of its library is still accessible via Veridian’s website.
Discover The Best Dark Web Links Of 2023
SecureDrop is an open-source platform that facilitates secure communication between whistleblowers and journalists. Developed by the Freedom of the Press Foundation, the dark web site allows users to privately submit documents and sensitive materials without revealing their identity. Insights like these help researchers and advocates understand how and why Tor is being used. With this info, the wider online community can grasp Tor’s impact and its ability to provide secure and anonymous internet access.
The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service. This ensures greater security and privacy, making it much more difficult for snoopers to get in. Hence, even if you hide your IP address, you aren’t completely secure.
We And Our Partners Process Data To Provide:
The Silk Road was a marketplace on the dark web that launched in 2011, where you could purchase all sorts of illegal goods. The vast majority of transactions consisted of illegal drugs, but you could also find weapons, personal information, child pornography and stolen credit card details. Allegedly, it was also possible to hire hit men on the site, though it’s never been proven that any of these contracts were actually fulfilled. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes. This means that if you do anything illegal on the dark web and are unlucky enough to be routed through one of these nodes, the authorities will be well aware of what you’re doing. Sites stored in the index are then ranked based on a variety of different factors, which is what decides how far up on the results page the sites appear in a search.
To understand the Tor or Onion search engines, one should learn or know what a search engine is and how a regular clearnet search engine works. Whether you’re looking for personal advice while shopping on the dark web or you want to discuss a wide range of topics, Dread has you covered. And unlike Reddit, this darknet site offers its users complete anonymity.
Final Words On Dark Web Search Engines
Regarding the quality and the update, they don’t have any updates from the release. They have only a single version of the search engine—an outdated search engine with more results. Haystack just might have the most indexed dark website on any dark web search engine at over 1.5 billion indexed pages.
Subscribe To Our Blog For More News And Updates!
However, time has changed, and now several services offer free dark web access with the least amount of technical knowledge. Since activists, journalists, and advocates need the dark web to communicate securely, find evidence, and bypass censorship, it remains a tool for privacy and free expression. Google is the reigning leader of spartan searching and is the most used search engine in the world.
Intelligence x is one of the best archival services and search services that we have to access online. Not only does it archive historic versions of websites online but it also includes leaked data that is typically removed quite quickly these days. Although this may sound a little similar to what Internet Archive’s service offers, Intelligence X offers some pretty cool differences. No matter how controversial the data leak, Intelligence X seems to not worry too much, providing it public for the masses, forever. The dark web often conjures images of shadowy corners of the internet, filled with intrigue and danger. Contrary to popular belief, it isn’t all illicit dealings and clandestine exchanges.
Benefits Of Using Forest VPN
- Finally, once the information has been searched, and collected, including the connected relevant information, someone needs to group this all together.
- When you access an onion site, your connection is routed through a series of nodes, each adding a layer of encryption.
- Damir earned a bachelor’s degree in physics, which he believes has given him the critical thinking skills needed to be successful in the ever-changing landscape of the internet.
- It can identify interesting public information on an organization’s computer network, by looking outside the fence.
- Before you start browsing websites on the dark web, make sure to protect yourself by using a VPN, proxy, or Tor.
- But like many other allegedly illegal search engines, the Hidden Wiki does index certain shady sites that Google blocks.
The dark web is a part of the deep web that contains websites not included in the mainstream search engine index. Accessing the dark web is legal in itself; the nature of the activities you engage in ensures it stays that way. Criminals prefer the dark web because it offers anonymity like never before. But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall. You can access almost any published paper that would have otherwise been hidden behind a paywall.
The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more.
Dangerous Software
Thanks to these characteristics, users have the choice to view material while remaining anonymous. Haystak is a dark web search platform specifically crafted for the Tor network. It catalogs about 1.5 billion pages, encompassing over 260,000 websites, making it a resourceful engine.