Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. Great life advice, but it’s even more valuable where the darknet is concerned. Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise.
Setting Up I2P (Invisible Internet Project)
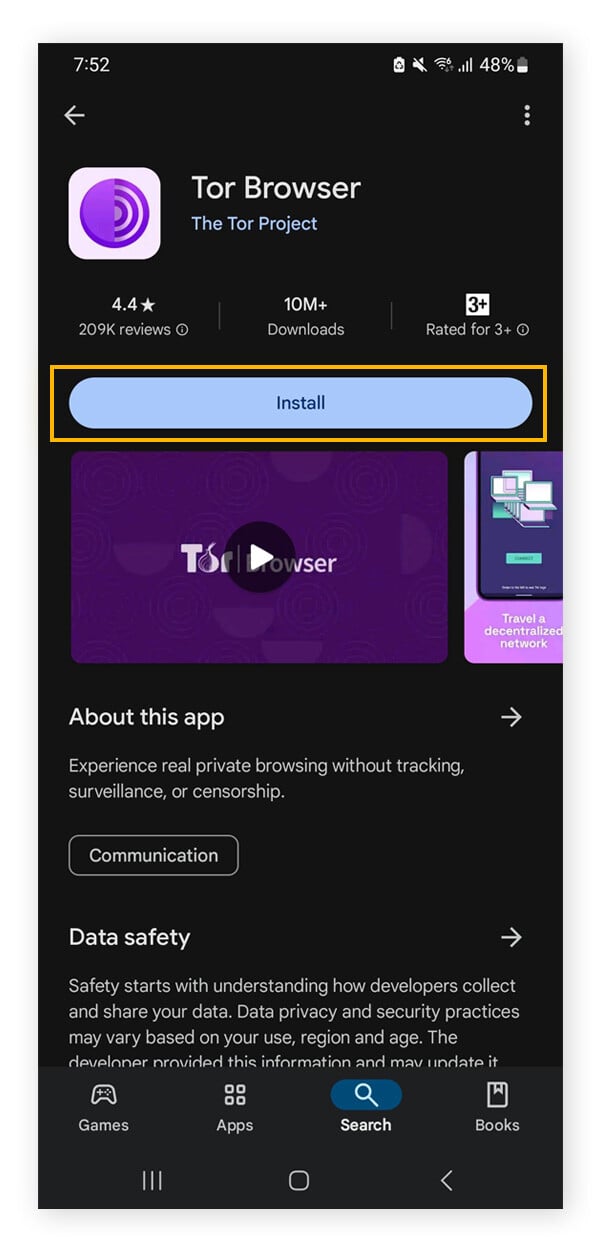
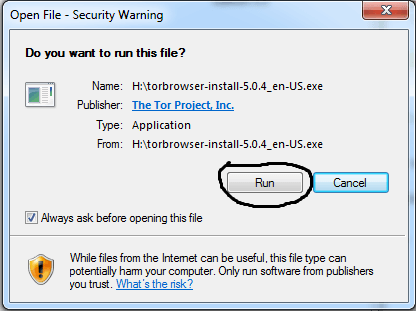
All users who create a new Webshare account automatically receive 10 free (shared datacenter) proxies + 1GB/month bandwidth to use for as long as they want, no credit card required. The user who signs up will get a free basic plan, and also have a 25% discount when upgrading. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship. The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship. One of the great things about Tor is that it can be used to access both the dark and surface web. Just note that although you’ll be anonymous, you won’t have the speed or convenience of a direct connection, and some sites might block you outright.
Whonix OS: Advanced Security Through Isolation
Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. I2P can only be used to access hidden sites that are only available on the I2P network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor.
Regularly Update And Configure Security Software
It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
This will help you navigate the dark web safely while staying out of markets you don’t want to come across or engage with. While there is a lot of criminal activity on the dark web, there’s nothing actually illegal about accessing the dark web. In certain countries, the dark web facilitates political discourse and conversation that would otherwise be censored, outlawed, or eradicated in entirety. While there are some threats on the surface web, and users need to browse with some level of security awareness, it’s a lot easier to stay safe on the surface web than the dark web. Staying cautious is essential when interacting with content on the dark web, as illegal activities are prevalent. Users should refrain from clicking on unverified links and exercise discretion in revealing personal information.
Best 10 Dark Web Browsers For Anonymous Deep Web Surfing
Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. The Tor Browser prevents your ISP from seeing what websites you’re visiting, but it does not prevent the ISP from seeing that you’re using Tor. Remember, the Tor browser connects to the internet differently than regular browsers in an attempt to increase your anonymity online. For example, legitimate sites, such as the BBC, the New York Times, ProPublica, and Facebook, have made their sites accessible as a Tor Onion URL to help people avoid government censorship. Whonix is a privacy-focused browser that operates in a virtual machine environment, creating a highly secure browsing experience on the dark web.
How To Access The Dark Web Safely: A 2025 Beginner’s Guide
In 2025, as governments and corporations intensify their surveillance capabilities, the importance of secure, private access to online information has never been greater. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL.
Monitor Your Traffic Routing
The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). Typically, any reference to the visible web will be to common websites with a familiar internet domain extension.
- Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
- While Tor makes it significantly harder to trace online activities, it does not guarantee complete anonymity.
- Be cautious of random or obscure links — these could lead to dangerous or malicious websites.
- The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
It’s simply a part of the internet designed to offer anonymity and privacy. While it does host illegal activities and shady content, it also supports legitimate uses like secure communication for activists, journalists, and whistleblowers in oppressive regimes. The dark web itself is neutral; how people use it is what makes it good or bad. Additionally, configure your security settings to provide maximum protection, such as firewall activation and using a VPN, while browsing the dark web.
- PIA doesn’t pull punches, so it strikes back against its competition with a proven-in-court no-logs policy, split tunneling, and even port forwarding to diversify its apps.
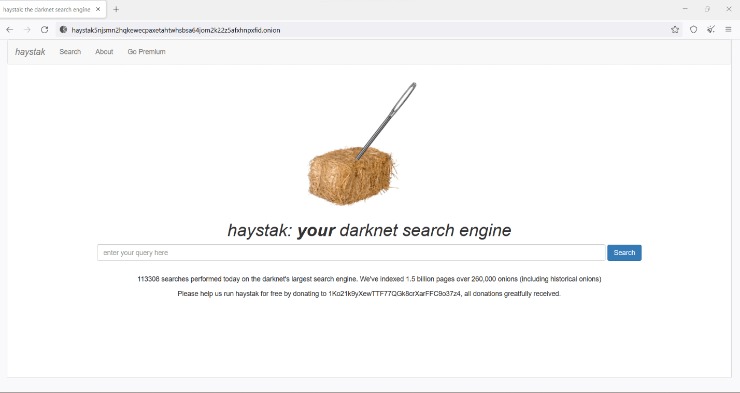
- You’ll need a specialized dark web search engine, like Ahmia or DuckDuckGo’s Tor service, which can help you locate onion sites (also called Tor sites).
- Many experts advise against using third-party mobile browsers that utilize the Tor Network.
- All Tor Browser data is encrypted and relayed three times over the Onion Router network, which is composed of thousands of volunteer-run servers, which are known as Tor relays.
- Google considers the majority of the content on the entire web highly irrelevant and useless to its users.
- The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
Take Extra Security Precautions
To access the dark web, one would need to use a special anonymous browser called Tor. Tor provides users with a higher level of privacy, which is particularly attractive to threat actors, cybercriminals, hackers, and government operatives who want to keep their identities secret. If you want to be extra safe, routing your connection through a VPN and then accessing the dark web using the Tor browser provides more security than Tor alone.
Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services. In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network.
In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. That means that only 0.024% of all the known pages are findable in Google’s search engine. The users only have access to a fraction of the available data and web pages. The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo.
PIA is popular in the USA because it offers servers in all 51 states. People in the United States and abroad can use it to venture into the dark web in privacy. With RAM-based servers in 90+ countries and features like WireGuard, IPv6 leak protection, and a kill switch, worries are over.
So, you should never share your personal information on the dark web. What’s more, they can also sell you personal information on the dark web as your personal data has a monetary value on the dark web. You should never trust websites and forums on the dark web with your personal information.
And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. I2P is a private network built for secure, anonymous communication. Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation.