• Get to know the terminology of the marketplace, rules and seller reputation scores. One of the hardest parts of the dark web, in fact, is finding reliable marketplaces. The dark web mostly uses decentralized network like Tor Project
How To Sell Counter-Strike 2 Skins Instantly? A Comprehensive Guide

Paste the URL of the darknet market into your Tor browser bar and hit enter. Some DNMs will load quickly, while others will load slowly or not at all. If the site hasn’t loaded after 30 seconds, refresh it or try an alternative site. Whether you’re a student seeking study-enhancing nootropics, or a septuagenarian with limited internet skills but a need for pain relief, this article is for you. In this example, we’re going to run through the steps for purchasing CBD oil off the darknet, but the same procedure can be used to acquire any one of the several thousand items listed on popular DNMs. With proper monitoring resources, you can gain visibility into threat actors and their activities.
🛡️ How Axis Intelligence Strengthens Cybersecurity
The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident. All payments on the platform are via Bitcoin (BTC) and Monero (XMR) for anonymous transactions. Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again. To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring.
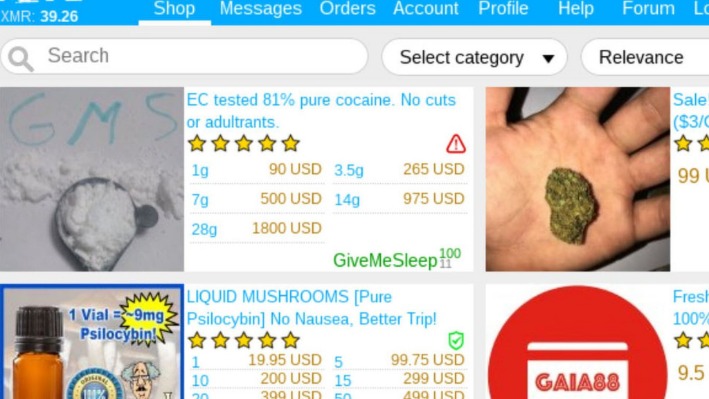
Specializing in brand building, product marketing, communication and content. If you decide to venture to the Dark Web and browse the markets, don’t buy anything. Remember, everything that’s being sold is illegal and most likely dangerous. Using a search aggregate, Cybereason Labs recently uncovered all kinds of interesting and illegal merchandise without logging into any market. Take the first step toward securing your business by exploring our solutions on Cybernod.

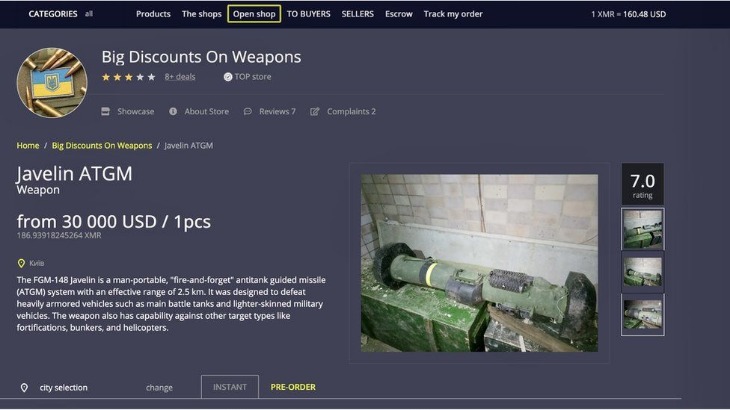
The Marketplace As An Arsenal
If you’re a beginner, and would prefer an easier way to buy bitcoin, you could install the Bitcoin.com Wallet, available for Android or iOS. Follow the setup instructions, including making a copy of the 12-word wallet recovery phrase that’s shown on-screen. Click the green ‘Buy’ button in the top right of the screen, select ‘BTC Bitcoin Core’ and then the amount in fiat currency you wish to buy (e.g. $50).
Users Are Largely Younger Men
Here, every deal happens without revealing real identities, and everything is kept secret with the support of tech-designed layers. This secret part of the internet runs on a mix of advanced tools and clever hacks. It raises real questions about trust, safety, and how we see privacy in a digital world.
Step 4: Create An Account
There are many VPN providers to choose from, but some of the most popular ones for darknet users include NordVPN, ExpressVPN, and CyberGhost. Make sure to choose a VPN that has a strict no-logs policy and supports the Tor network. Some researchers who study the dark web have found the quality of drugs available on these hidden websites is superior to that of drugs sold on the street. One theory of why that might be is that the online review system holds dealers accountable, says Rasmus Munksgaard, a Montreal researcher. He was equally compelled by the system of vendor and product reviews. Similar to legal online retailers, dark net drug listings feature dozens of reviews, assessing the products for quality, purity and shipping times.
Good Password Ideas And Tips For Secure Accounts
The stolen credentials allowed attackers to infiltrate the company’s email system, impersonate senior staff, and send fraudulent invoices to clients. Within days, the attackers had exfiltrated sensitive client information, including proprietary marketing plans and billing data. Implementing strong authentication protocols, such as multi-factor authentication (MFA), significantly reduces the risk of unauthorized access. MFA requires users to provide multiple forms of verification, such as a password and a one-time code, making it more difficult for attackers to exploit stolen credentials. Note- If someone is interested in using darknet markets, it’s very important to know the risks. Without the right knowledge and safety measures, they could face serious problems.
- This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page.
- Failing to monitor these underground forums can expose companies to financial losses, reputational damage, and compliance violations.
- The platform’s popularity continues to grow, attracting both new and returning customers.
- The other enabler, of course, is the maturation of info-space that allows these marketplaces not to exist in a physical place.
- Below is a neatly tailored list of the products and services that you can grab on the dark web using cryptocurrencies.
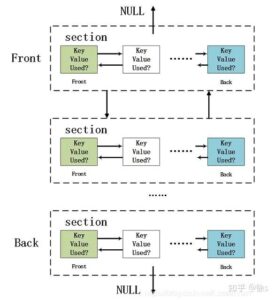
The proliferation of cloud services means everyone’s becoming more comfortable with virtual private servers. So the info infrastructure is also helping people to be able to do these things. Darknet users have to install specialised software that uses countermeasures such as cryptography so it makes it hard for people to trace them. You’ve got your internet, which allows us to all connect with each other, and the darknet is a space you can use with what we call a gateway service to connect to what is essentially another network. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P.

Before you can buy from a darknet market, you will need to create an account. This process typically involves providing an email address and choosing a username and password. Some markets may also require you to provide additional information, such as your real name or address. It is important to note that providing false information can result in your account being banned or your purchases being seized. There are media websites on the dark web—both legitimate and illegitimate—that allow users to access digital media outside the highly monitored surface web. As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content.
Threat intelligence gathered from the Deep and Dark Web is likely to help future threat hunting teams when analyzing telemetry from beyond their own networks, such as the Deep and Dark Web. As stated earlier, neither of these connected content repository networks are illegal to access. Indeed, they must frequently be accessed by cybersecurity organizations conducting threat hunts or defending their networks or those of their clients. So, believe it or not, it’s not illegal to access the Dark Web; there are actually reputable brands and companies who have sites accessible via the Dark Web. It can simply be a dangerous proposition to peruse the Dark Web and engage with whoever you may meet, especially if it means revealing any personal data.

Market Value And Popularity

Even platforms like Netflix, which require paid access, are technically part of the Deep Web. You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses. Search engines like Google, Bing, and Yahoo can access just about 4% of the web.