Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
Navigating Safely: The Role Of Forest VPN
Everyone can contribute to protecting vulnerable individuals by staying informed about warning signs and utilizing official reporting channels. Support organizations maintain strict confidentiality protocols to protect survivor privacy while providing essential services for recovery. Mental health professionals collaborate with law enforcement victim specialists to ensure comprehensive care coordination.
Always double-check the spelling of a link and compare it against a trusted directory or the official announcement thread (if available on Dread or Reddit). Avoid clicking links posted on surface web comment sections or unverified forums. And never bookmark .onion links unless you’re sure they come from a trusted, PGP-signed source. To explore dark web sites that are safe in 2025, combine the right tools with smart browsing habits. Verified directories, anonymity tools, and cautious clicking make all the difference.
Reporting Criminal Activity Online
There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. The good news is that the platform will not see what you copy/paste.
- The availability and accessibility of CP can distort societal attitudes and contribute to an environment where child exploitation is tolerated or normalized.
- For recommendations on choosing a VPN, look for expert reviews and articles.
- This lets you check what information it contained at a previous point in time.
- Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web.
Shareable Text-based Detection For CSAM
It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region. Deep Search is an open-source dark web search engine designed to index and explore onion space, the hidden services within the Tor network. Known for its accuracy, Deep Search stands out by delivering precise and useful results, avoiding the spammy links commonly found on similar platforms.
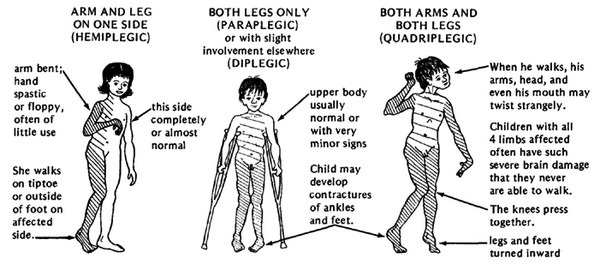
A large portion of this group is likely to have sexual interest in children (i.e., paedophilia or hebephilia)4. These sexual preferences are classified as mental health disorders because they result in self-harm and harm to others, and therapy can improve well-being and prevent harm to children5. AVG Secure VPN encrypts your internet traffic and obscures your IP address every time you use it to go online — dark web or not. With a variety of server locations around the world to choose from, you’ll be able to navigate the web more privately and access the content you want.
🌐 What Are Dark Web Sites And Links In 2025?
Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store.
Dark Web Search: The Best Dark Web Search Engines In 2025
Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information. These pages can also help circumvent some forms of government censorship. Yes, there are numerous legal and safe .onion sites, such as The Hidden Wiki for directories, ProtonMail for encrypted email, and SecureDrop for whistleblowers, among others.
Tor’s Most Visited Hidden Sites Host Child Abuse Images
Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.

You can never be sure who’s really behind the other end of the line. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users.
- For example, it maintains your privacy and enables you to access untraceable content and services.
- Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites.
- Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
- This is effective, as the vast majority of onion websites are written in English, and search data indicates that almost all users seek explicit material using English terminology.
Hidden Service Lists And Search Engines
Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator.
It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. Traffic to hidden services on Tor represents about 1.5% of all the data passing across the network on any given day. The inclusion of implicit terminology would give rise to ethical concerns about censorship.