Some services are genuine; you can get what you want at an agreed fee. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.

Darknet Markets Explained: Navigating The Hidden Web
A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity. Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN.

Data Breaches Through Contractors
You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users. It’s a market for fake documents, hacking software, and financial fraud services. WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. These marketplaces are full of risks (security, legal, ethical issues – all of them).
Best Onion Sites By Category
For starters, I’ve only included the very old, established single-vendor markets. In most cases, the vendors also have deposited large amounts for the vendor accounts. This is returned only if the vendor doesn’t scam people and isn’t reported multiple times. Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down. It issued a press release revealing that, from December 2021, the website won’t be functional anymore. mark it means it has been verified as a scam service and it should be avoided. We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats.|The reason was to protect US intelligence communications online. Yes, you can access the dark web on mobile — you just need the right app. Android users need to download the Tor Browser app, while iPhone fans should get the Onion Browser app. Many dark web search engines are available, and no single option is objectively the best. ZeroBin’s onion address ensures your traffic is routed through multiple nodes, so it’s challenging for any third party to trace any message back to your original location.|Finally, product variety significantly influences marketplace choice. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing.|As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. This can be stopped if law enforcement agencies can break any link, particularly dark web marketplaces, in the chain. Hence, it should be the top priority to track these platforms and shut them down as quickly as possible.}
Such content fuels a dangerous cycle of abuse, violence, and exploitation. These hackers don’t hide in the shadows as much as you might think. In fact, many openly advertise their services on darknet forums.
- Kaspersky DFI researchers observed more than 11 hacktivist movements and various actors across the region.
- Forums and magazines play a crucial role in keeping users informed about new market links and updates.
- Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
- Confidential government files and pages tied to unlawful trafficking often get filtered out.
- The platform’s popularity continues to grow, attracting both new and returning customers.
Security And Anonymity Features
BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself.
All that one can expect from a deep web marketplace when it comes to anonymity and security. Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy. SecureDrop is an open-source platform that facilitates secure communication between whistleblowers and journalists.
Can You Be Traced On Tor?
Like other marketplaces, it also requires registration for new users and accepts payments in Monero. You can tell you’re on the dark web if you’re accessing websites with .onion addresses on the Tor Browser or a similar anonymity network. These sites aren’t accessible via standard web browsers or search engines. Unlike traditional search engines, it doesn’t track or store personal information, ensuring your searches stay private. It’s a popular choice for users worried about online surveillance and data collection. However, when it comes to darknet markets, the story is very different.
Malicious Software
Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security.

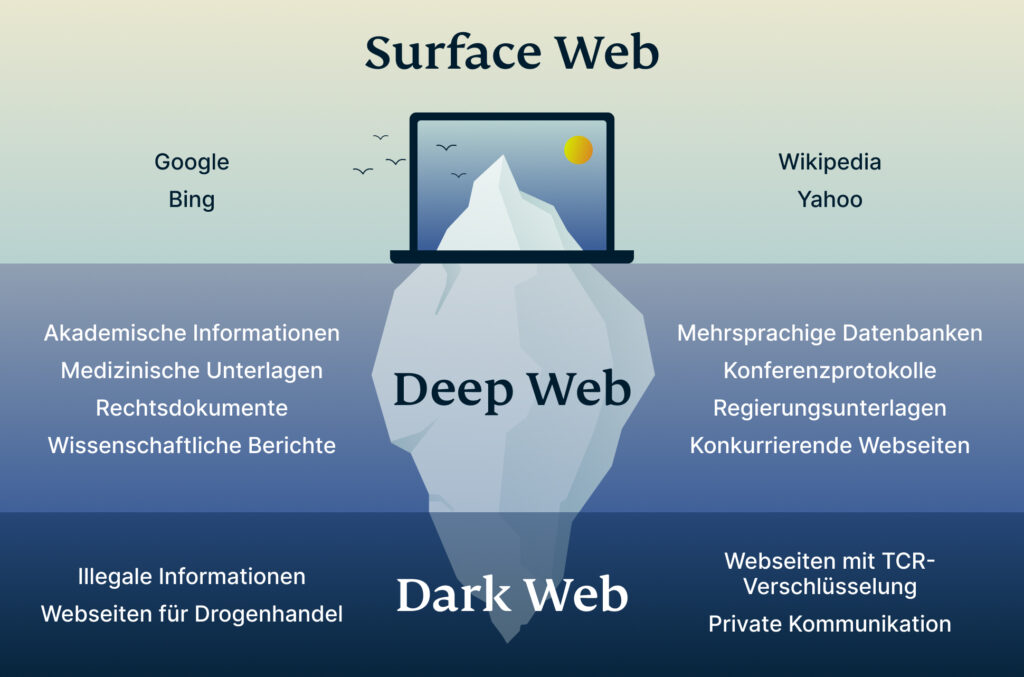
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it.
Top Darknet Marketplace
This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media. The website’s articles focus on digital rights, surveillance, and security research. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. To keep a closer eye on your personal information, you can use services like NordStellar’s dark web monitoring.
For instance, after the closure of Genesis Market, its website came back after a few weeks. As mentioned earlier, launching a cyberattack doesn’t require any hacking skills. Even people with zero technical knowledge can buy phishing kits, ransomware, or stolen logins. Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns.
Dark web links can change frequently, so always verify addresses from multiple trusted sources before visiting any .onion site. The links shared in this guide were working during testing, but legitimate services occasionally move to new URLs to enhance security. I recommend bookmarking verified links rather than relying on search results. Pitch is a dark web-based Twitter/X alternative, providing a secure platform for anonymous discussions and information sharing. Unlike many dark web platforms, it maintains strict content guidelines while protecting user privacy. TorLinks maintains one of the most reliable directories of verified .onion sites.
Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails.



