Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content. To keep a closer eye on your personal information, you can use services like NordStellar’s dark web monitoring. This solution scans dark web forums to alert you if your data is being listed, traded, or otherwise exposed. The dark web alert system is designed to urge you to take action before any significant harm is done. Cybercriminals can rent or buy malware tools through darknet markets. This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves.
What Exactly Is Sold On These Marketplaces?
The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. This means that using the dark web may attract attention from your ISP or even law enforcement. To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as an extra layer of protection.
- Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices.
- It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers.
- Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden.
- The layers of encryption hide your data and activity from snooping eyes.
- Also, the platform has a feature of automatic deletion of messages – set a timer and they will be deleted after a set period.
Popular Dark Web Marketplaces
Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight.
Best Dark Web News Sites Offering Factual Information
Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web.
Criminal Hacking Services
These products are often sourced from international suppliers, ensuring competitive pricing and a wide variety of options. Digital products, such as e-books, software, and online courses, also play a significant role in the ecosystem, catering to a diverse audience. The use of cryptocurrencies like Bitcoin and Monero remains central to the darknet ecosystem, providing anonymity and reducing the risk of financial tracking. Additionally, the rise of decentralized marketplaces minimizes the risk of shutdowns, offering users a more stable environment for trade. In conclusion, the darknet continues to evolve, providing a secure and efficient platform for drug trade.
It’s great how the site has a Security Scenarios section too, where it offers personalized security tips for specific audiences (activists, academic researchers, journalists, and more). The Hidden Wiki is the best way to start browsing the dark web because it contains dozens of links to popular .onion sites. Compared to its predecessors, Archetyp enforced enhanced security expectations from its users. These included an advanced encryption program known as “Pretty Good Privacy” and a cryptocurrency called Monero. Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default, which makes them nearly impossible to trace.
Tweak Tor Browser Settings
On the dark web, even a minor slip-up can cause you big consequences. So, you need to be extremely cautious because the fake sites are often very similar to the real ones, making them dangerously convincing. Still, the existence of this content is a grim reminder of the dark web’s potential for abuse when left unchecked. One notable fact is that the site has changed its domain twice since its formation. Today, Exodus Marketplace works from 3 different domains, two of which are its mirrors.

FAQs About The Dark Web And The Websites That Live On It

Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes. Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks.
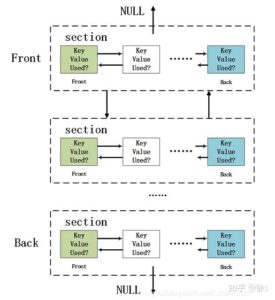
Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name. When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection.
Using Escrow And Trusted Mediators Where Possible

Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. It contains a good selection of product listings that range over 35,000 items. The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security.
II Security And Anonymity On The Dark Web
When you try to enter a .onion website, it will reroute your access request around the internet, bouncing it off three random servers before you reach the target website. Like regular browsers with domain names, the Tor browser also has its own domain designation. These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. This is no different from the “.net” or “.com” of the regular Internet. So, whether you seek refuge from oppressive regimes, are searching for answers to hard or embarrassing questions, or are trying to share confidential information securely, there is something for you. In today’s digital era, where information is constantly on the move across all digital platforms, an…
The integration of advanced encryption technologies and decentralized systems ensures that transactions remain confidential, while user feedback mechanisms enhance trust among participants. The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and reliability. By 2025, several platforms have emerged as leaders in this space, leveraging advanced encryption, decentralized systems, and user-friendly interfaces to ensure seamless transactions. These advancements will further solidify their position as a secure and reliable option for users worldwide.