Perhaps you fell for what seemed like an innocent text requesting your date of birth and that...
For instance, BidenCash saw a surge in user activity following its free data leaks. If you’re unable...
When investigators searched the homes of the individuals involved, counterfeit notes were found in the two 16-year-olds’...
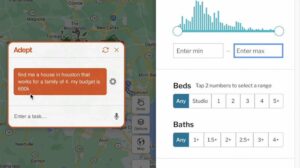
At CNBC Select, our mission is to provide our readers with high-quality service journalism and comprehensive consumer advice...
Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves....
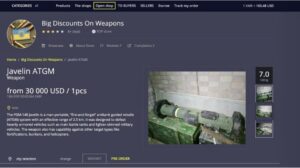
The selection depends on the marketplace, and not everything found is legal. In addition to counterfeit merchandise,...
Be disciplined in keeping privacy policy etiquette and best practices. In addition to these measures, you have...
Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred...
Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets...
While an endpoint security program can identify such threats if they end up on your computer, it’s...