Blockchain uses a shared and unchallengeable record that authorized members can only retrieve. The network members rheostat what info each member may grasp and what actions they can take. Nodes store and propagate the network payments’ state efficiently, going straight from one person to another. BTC is the first and most extensively known digital cryptocurrency created in 2009 by an unknown person using the codename Satoshi Nakamoto.
However, engaging in illegal activities while on the dark web remains unlawful, just as it is in the real world. Security should always be your primary concern when selecting tools for accessing the darknet. Remember that no single tool provides complete anonymity – it’s the combination of proper tools and practices that ensures safe access. Onion websites use onion routing, a technique for encrypting and anonymizing data transmitted over the Tor network. The name “onion” comes from the layered structure of the encryption, similar to the layers of an onion. These websites are not accessible via normal web browsers, but require special software such as the Tor browser.
Best Dark Web Websites

It’s one of the few resources that consistently updates its .onion mirror, ensuring availability even during domain seizures or censorship events. One of the simplest, most censored, and biggest search engines on the deep web. It provides all types of search result and URL that helps users find their result swiftly. The homepage stinks easily and boasts progressive features like searching only for titles or URLs.
- These services form the communication backbone for sensitive conversations in high-risk environments.
- But people can still access independent media via BBC Tor Mirror and similar dark web news portals.
- While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams.
- Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it.
- The Tor network adds a layer of anonymity, which helps dark web sites remain hidden and makes it impossible for conventional search engines to index them.
- For any book or article that you want to read, you get a collection of online libraries that have it with them.
🌐 What Are Dark Web Sites And Links In 2025?
George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years. He has worked for several international tech platforms, and his writing and editing expertise has also enhanced over time. He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words.
Search Code, Repositories, Users, Issues, Pull Requests

Proton also offers other security tools besides ProtonMail, such as Proton Drive, Proton Pass, Proton Calendar, and Proton VPN. It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for. However, the threat of clicking on the wrong link always remains, so be cautious while you use it. Just like Facebook, this is no random namesake; it is a legitimate platform from which to reach the CIA anonymously.
Choose a trustworthy VPN service that has a strict no-logs policy and supports connection without DNS leaks. Avoid free VPNs as they often lack adequate security or monetize user data. Users turn to the Hidden Wiki because it simplifies navigation through the complex and often confusing dark web. Many people seek it out for privacy and anonymity, as the Tor network and the Hidden Wiki help mask identities and activities from surveillance. Furthermore, the Hidden Wiki plays a critical role in censorship resistance, providing uncensored content and services that might be blocked on the surface web.
SecureDrop, meanwhile, enables whistleblowers to send files to journalists anonymously and securely. These platforms are trusted by activists, reporters, and individuals in oppressive regimes who need to share sensitive information safely. OnionLinks is a curated dark web directory updated frequently with working .onion URLs.
- Its affordability and reliability have earned it a loyal customer base.
- Tor Network, short for “The Onion Router”, is a network consisting of volunteer servers that encrypt Internet traffic and route it through multiple nodes.
- Its anonymous nature enables users to create and submit encrypted documents, chat securely, and receive private responses from journalists.
- All vendors are vetted before they are allowed to sell, so it makes sure of trust and quality.
- The advantage of this version is that you can effectively create a Facebook account anonymously or use this social media platform in a restricted region.
- Always remember that accessing certain darknet content may be illegal in your jurisdiction.
✅Final Thoughts – Stick To Known, Safe Directories

Even a single wrong character in a .onion A URL can lead to scams, malware, or fake marketplaces. That’s why relying on trusted onion directories like Ahmia, Dark.Fail, OnionLinks — and the real Hidden Wiki — are essential. ZeroBin allows users to post encrypted text that even the host server can’t read — perfect for pasting links or messages securely. OnionShare lets users share files directly from their device over a temporary .onion address without needing a centralized server.

Dread is the most active, functioning like a Reddit-style message board where users discuss everything from Tor security to reviews of dark web services. Hidden Answers, on the other hand, is more like a dark web version of Quora. It allows anonymous users to ask and answer questions on controversial or privacy-sensitive topics. Both are valuable for learning and exchanging ideas without revealing identity.
Dark Web Links: The Best Onion And Tor Sites In 2025
The links shared in this guide were working during testing, but legitimate services occasionally move to new URLs to enhance security. I recommend bookmarking verified links rather than relying on search results. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found.
Email Services
Therefore, if someone is willing to buy, you must have protective layers in your device and browser. It safeguards your different devices and a network that you can use to transfer the info. But some might consider investing in a paid VPN because they are using free VPN version, which may be quite risky.
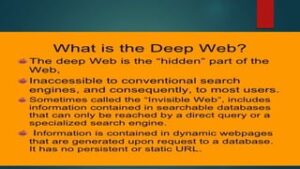
The deep web, often misunderstood and shrouded in mystery, is a vast and mostly uncharted section of the internet. Unlike the surface web, which is accessible through standard search engines like Google, the deep web includes a range of content not indexed by these engines. Within this complex web lies the dark web, a small but significant part of the deep web that requires specific tools such as the Tor browser to access. Here, anonymity reigns supreme, and while the dark web is infamous for illicit activities, it also hosts valuable privacy-focused resources. Exploring this space requires caution and the right tools to ensure safety and privacy. When it comes to accessing darknet links safely, choosing the right tools can make a significant difference in your security and anonymity.
Onion_Endpoints_Fetcher
Some users also share links on encrypted apps like Telegram or Keybase that you can check. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Unlike other search engines, it does not collect or share web activities and personal data of users.
Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.