While a VPN adds valuable protection, being selective about which sites you visit and never sharing personal information are equally important. Stick to verified dark web directories and legitimate services to minimize your exposure to risks. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. DuckDuckGo’s dark web version offers the same privacy-focused search experience as its clear web counterpart.
Verified Social Channels And News Sites
- The dark web is neither entirely a haven for illicit activities nor a utopian space of limitless freedom.
- Info like your name or email address never needs to be shared on the dark web.
- I also recommend using an antivirus (like Norton 360) to protect your device from malware infections.
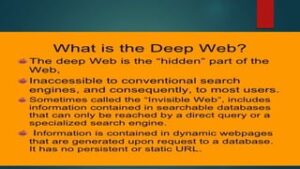
- The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now).
- We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals.
With this in mind, it is essential that you are careful about what you choose to visit and where you choose to click. As always, we strongly recommend using a reliable antivirus and a robust VPN to increase your security. For this reason, it is always better to use a trustworthy VPN for Tor while accessing the Dark Web, as this will provide a robust additional layer of privacy. The Tor network is designed to provide you with privacy and anonymity.
Introduction To The Tor Network: Security And Privacy
As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with.

Other options include Ahmia and NotEvil, which focus on listing .onion links. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Legitimate Use Cases For The Average User
Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy.

Why Is Tor So Slow?
Today, buyers and vendors look for reliable alternatives that offer security, escrow protection, and a strong vendor community. Payments are made with digital money, which helps protect the identity of both the buyer and the seller. This use of cryptocurrency makes transactions fast and secure, and it supports the overall goal of privacy on the dark web. The key differences between dark web markets and regular online stores are clear.
Dark Web Forums You Need To Monitor For Improved Cyber Security
However, there’s also a high prevalence of illegal activities, so caution is advised. The dark web marketplace links hold the potential for both risk and reward. By taking precautions and using tools like Forest VPN, you can explore this part of the internet safely. Remember, the key to a secure experience is vigilance and the right technology.

However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. While no approach is foolproof, a thoughtful, criteria-driven strategy ensures a more secure and beneficial experience on the dark web. No, it isn’t illegal to browse the dark web, and there’s nothing inherently wrong with visiting a Tor website.
More On Tor Onions
There are media websites on the dark web—both legitimate and illegitimate—that allow users to access digital media outside the highly monitored surface web. As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content. Hacking and cybercrime forums on the dark web are spaces for newbie hackers to ask questions, veteran cybercriminals to share their expertise, and buyers to find sellers. Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums. There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data. Learn more about the kinds of sites that can be found on the dark web and how you can access them.
Dealnews also has an extensive news section under the “Blog” site header, with much of its content produced by in-house retail experts. It’s a great source of information and news about the retail industry in general, including consumer protection issues applicable to your purchasing decisions. Discounts and coupons range from 80% to 90%, all from third-party retailers. Dealnews sets itself apart with detailed deal listings that often include price comparisons, which are useful for shoppers struggling to properly value items they’re thinking of buying.
The selection depends on the marketplace, and not everything found is legal. Just as any other stolen accounts can be purchased from the dark web marketplaces, hacked PayPal accounts are also available for purchase in the various markets on the Tor Network. The vendors collect fund-filled PayPal accounts and list them on their product selling page. The buyers purchase them based on the funds available and the amount of crypto they are willing to pay for that account. After procuring the account from the darknet sites, the buyers drain the accounts on their will.
It doesn’t track your browsing history, location, or any other data. It’s so secure and privacy-oriented that the Tor browser uses it as the default search engine. Some sites are perfectly legit—such as domain services and email providers.
Separate Your Real Life From Your Online Persona
Monitoring the activity on these platforms is crucial for fraud detection, brand protection, and financial intelligence. Since then, BidenCash has continued to operate using the “dumping” method. This involves adding daily listings of stolen credit card details to the site and periodically dumping large amounts of stolen credit card details at the same time. In addition to these types of listings, there are other free tools usually available on credit card sites. ESentire’s Threat Response Unit has also observed AI integrated into the StealC admin panel to help filter stolen logs.