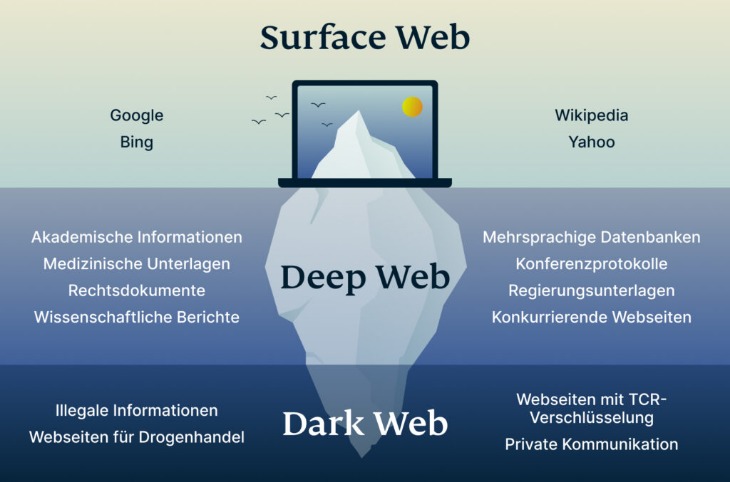
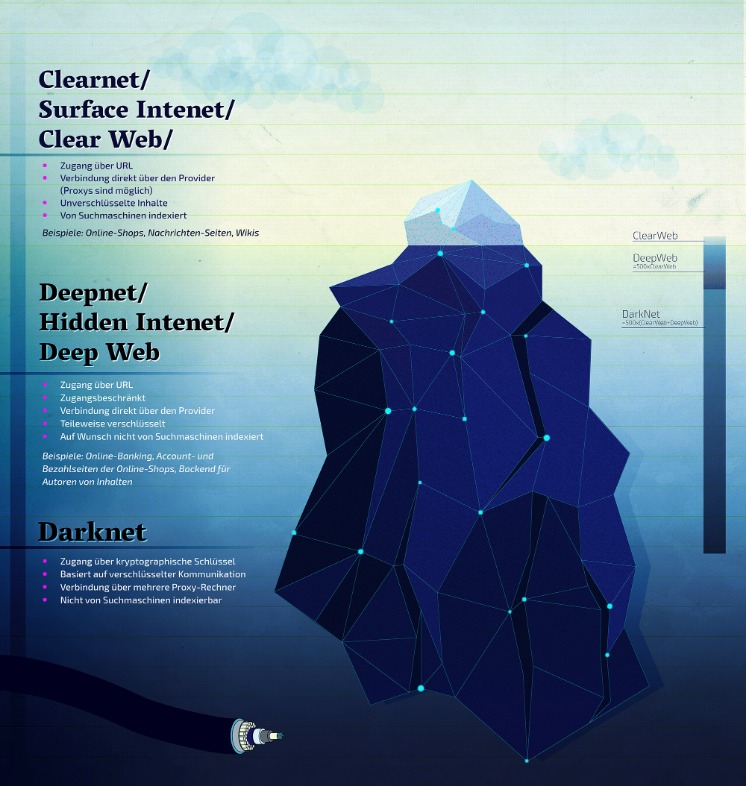
The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet.
Is It Illegal To Visit And Use Dark Websites?
For safer browsing, it is highly recommended to also use a VPN and antivirus software. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline. Always access the Hidden Wiki through the official Tor Browser, never via a standard browser.
- Try ZeroBin, a covert, dark web-based, communication platform that allows you to send media and text messages to your confederate.
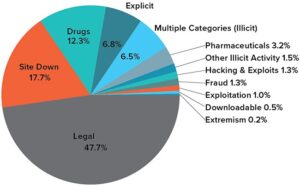
- A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material.
- We review and list tools and products without bias, regardless of potential commissions.
- Blockchain even has an HTTPS security certificate for even better protection.
- Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
Never Share Personal Information

The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. mark it means it has been verified as a scam service and it should be avoided. The Internet is a vast and complex landscape, much larger than the familiar interface we use every day. We are a passionate team dedicated to bringing you the latest news and insights. Our mission is to provide accurate, reliable, and engaging content that keeps you informed and inspired. Following the closure of Silk Road, various successor markets emerge, but none capture the same level of notoriety or impact.|Please note that not Evil does not tolerate adult content, narcotics / gun markets, or any other illegal content. These search engines are systems that list onion links from the deep web, the main task of each search engine is to allow the display of hidden pages. In contrast, .onion email providers are specifically designed for the Tor network.}
A Dark Web Search Engine

It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Discover everything about what a darknet market is, top marketplaces, security threats on them, and learn how to protect your data online.
Is It Safe To Visit The Dark Web On An IOS Or Android Device?
It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.
The 9 Most Private Cryptocurrencies In 2025
Since the Hidden Wiki can be a hotbed for scams, explain best practices for verifying links before visiting or interacting with them. Explore how the Hidden Wiki influenced the perception and culture of the dark web. It democratized access, making it more than just a tool for hackers or criminals — it became a place where privacy activists, journalists, whistleblowers, and everyday users could find resources. Educate yourself about basic operational security (OpSec) principles to minimize the risk of exposure or scams when using the Hidden Wiki or any dark web service. In 2025 and beyond, the Hidden Wiki still serves as a key resource for new and experienced users alike. It embodies the dark web’s values of privacy, decentralization, and open access, even as it wrestles with security challenges.
- Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device.
- The Onion Router (TOR) network hosts the dark web on its platform, allowing users to remain anonymous while using it.
- It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser.
- It should be noted that many of these services are illegal, and are neither condoned nor advised on this subreddit.
- You can also use its .onion link via the Tor network to access the site in restrictive countries, where it might be unavailable.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
Safety Precautions When Accessing The Dark Web
However, in June 2025, BidenCash’s relevant domains (around 145) were seized by the US Department of Justice. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market. It has been in operation for more than a decade since its debut in 2014.
However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
DuckDuckGo — A Dark Web Search Engine

Users can ask questions, share answers, and engage in discussions without revealing their identities. It’s maintained by a volunteer-run collective from the USA that protects the platform from malicious attacks and pledges to support social justice and progressive causes. Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception. Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week.
Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. Ahmia is a dark web search engine designed to index and search tor websites. This traditional search engine is also compatible with the dark web and can help you find dark web websites. You could try to visit a major site like Facebook’s onion site to check if your browser is working at all.
This was the initial framework for anonymous communication and file sharing. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials. There is no need to visit darknet marketplaces yourself to know whether your data was leaked. Still, even with these crackdowns and better defenses, dark web markets just keep coming back.
Facebook — Dark Web Version Of Popular Social Media Site
Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms. The fallout for victims whose data is stolen and sold can be devastating. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives.