However, users frequently face challenges in finding reliable and functional .onion links, as addresses can quickly become outdated, compromised, or deliberately shut down due to legal or technical reasons. In this guide, we’ll explore essential tools and best practices for locating and verifying working .onion links and their mirrors safely and effectively. One of the most frequently recommended security measures is to use a Virtual Private Network (VPN) in conjunction with Tor Browser, a practice often referred to as “Tor over VPN”. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. A VPN encrypts this initial connection, making it more difficult for the ISP to detect Tor usage. Some VPN providers offer “Onion over VPN” features, which route traffic through the VPN’s servers and then into the Tor network, providing a convenient way to access onion sites.
How To Get On The Dark Web Safely & Anonymously In 2025?
It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. The Hidden Wiki is a popular onion link directory on the dark web offering categorized lists of sites. Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script.
How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo

A secure VPN server slows down your browsing much less than the Tor Browser and also opens access to geo-blocked local content around the globe. This makes it a great option for watching videos from streaming services that are available only in other regions of the world. This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities. A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you.
Malicious Software
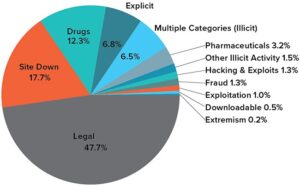
For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features.
No one can force you to visit a drug-selling site, give out your info, and buy cocaine or something else. As long as you pick your sites carefully and use a safe and secure VPN, you’ll remain untouched and be able to browse this internet space indefinitely. We understand that because of the reputation looming over the dark web as being so dangerous, mysterious, and whatnot. Some sites are safe to use, especially those where you don’t need to provide sensitive information to use. This provider’s performance is top-tier, with full Tor Over VPN support to make things simpler. Connect to ANY of its 3,000+ servers, open Tor, and do your magic!
The most common darknet software is the free and open-source Tor, short for the Onion Router. The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs). While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity.
- However, be careful when using the Tor Browser to access the dark web.
- Contact your country’s cybercrime division or law enforcement agency with evidence and information.
- It doesn’t track browsing habits or personal data and won’t expose a user’s identity or location.
- Additionally, there’s a unique reward system based on cryptocurrencies, and you can also use the built-in crypto wallet.
- The Tor Browser is a modified version of the Mozilla Firefox browser and includes the TorButton, TorLauncher, NoScript, and HTTPS Everywhere Firefox extensions, along with the Tor proxy.
- The market claims to provide secure and anonymous commerce services.
WANT TO TRY THE TOP VPN RISK FREE?
The dark web draws not only serious cyber criminals but also law enforcement agents aiming to catch them. Many exit nodes are actually operated by law enforcement and scammers. SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity. Many news publications (including many of the ones listed above) use SecureDrop on their .onion sites.

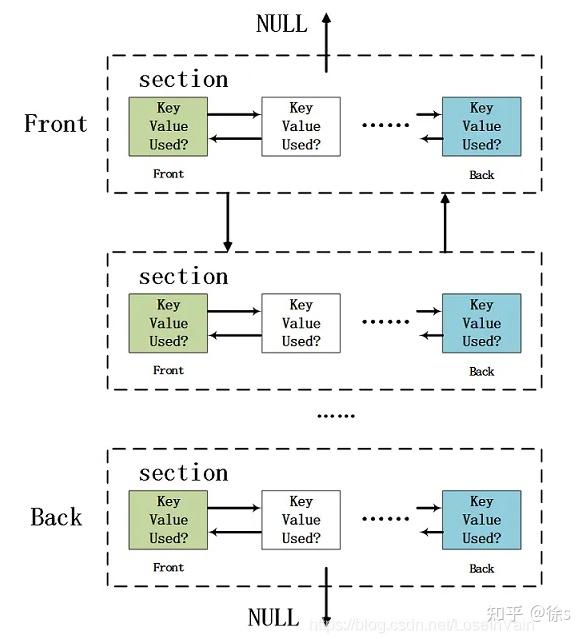
Subscribe To Our Newsletter
The links for listed services that are experiencing downtime or are no longer accessible will be highlighted in red as it actively tracks the uptime/downtime for all listed services. The dark web contains content that’s only accessible through networks like Tor. Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. The Onion Internet Protocol address (.onion) also replaces the actual IP address of the sender’s computer, meaning the physical location of the sender is also masked.
Tor allows you to circumvent these restrictions and get access to worldwide news, such as the BBC website shown below. Upon opening the Tor website, you will be presented with various download options for the operating systems that Tor supports, including Windows, macOS, Linux, and Android. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. The same general process applies to other operating systems, as Tor is also available for Mac and Linux. This method is called Tor over VPN, and it’s a great way to increase your privacy over using Tor alone. As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law.
Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. The Dark Web refers to hidden websites that aren’t indexed by regular search engines like Google or Bing. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. Now that your connection is active, it’s encrypted and untraceable by your internet provider.
- One of the earliest and most well-known of these is “The Hidden Wiki”.
- If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps.
- Of course, not all the popular and widely-used dark web sites and things like marketplaces on the dark net are illegal.
- Your online activity and communications remain private and secret on the dark web.
It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
Legitimate Use Cases For The Average User
Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server. For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely. By proactively avoiding these common pitfalls, you can significantly enhance your security and safely navigate the complexities of the dark web. However, if you’re looking to trade or buy something, the risk of scams increases exponentially.
It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime.
Archetyp Market
Many dark web search engines are available, and no single option is objectively the best. While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. Many dark web links could get you mixed up in some kind of criminal activity of another, whether you’re looking for it or not. The deep web is rife with sales of illicit drugs, weapons, and goodness knows what else, and steering clear of these nefarious web pages is easier said than done.
Are Onion Sites Safe?
You could do all your browsing with Tor, though it’s slower than a standard browser, something the Tor Project is working hard at to improve, says Stephanie Whited, communications director for the Tor Project. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual. Enable MFA wherever possible to protect your accounts from unauthorized access.