BTC and Monero accepted, with multi-signature escrow and global shipping—vendors love it, and I’ve seen why after snagging some rare stuff hassle-free. Drugs dominate, but digital goods are picking up—ties into the Telegram trend with side hustles. They’re talking AI search tools for 2025, which sounds slick—finding stuff could get way faster. Bohemia’s got a fresh feel since it started after Hydra went down. It’s all about drugs and digital goodies, with BTC and Monero on deck.

“Get Rich Or Keep Tryin’: Trajectories In Dark Net Market Vendor Careers ”, Booij Et Al 2021
Then, one of the neighbors is selected at random, and a new data point is created at a random point between the two listings in their feature space. It has a bidding feature, with new batches of stolen data being frequently added. Never log in with your real name or reuse passwords from other accounts.
Major Risks

With 2FA and escrow, it feels safe enough, and it rarely goes offline. In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends. Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
How To Access The Dark Web Safely

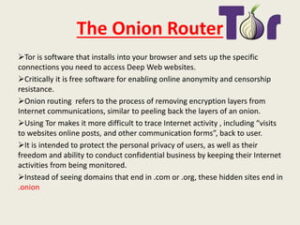
Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. You can archive any site you want, or retrieve historical records wherever available. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. This means that using the dark web may attract attention from your ISP or even law enforcement.
VPN Alternatives For Securing Remote Network Access
Known for its commitment to anonymity, it’s a preferred choice among darknet users seeking private and unbiased search experiences. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity.
Cyber-Attacks And Scams
Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets. Still, even with these crackdowns and better defenses, dark web markets just keep coming back. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities. Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky.
Tools & Links

Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar.
After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
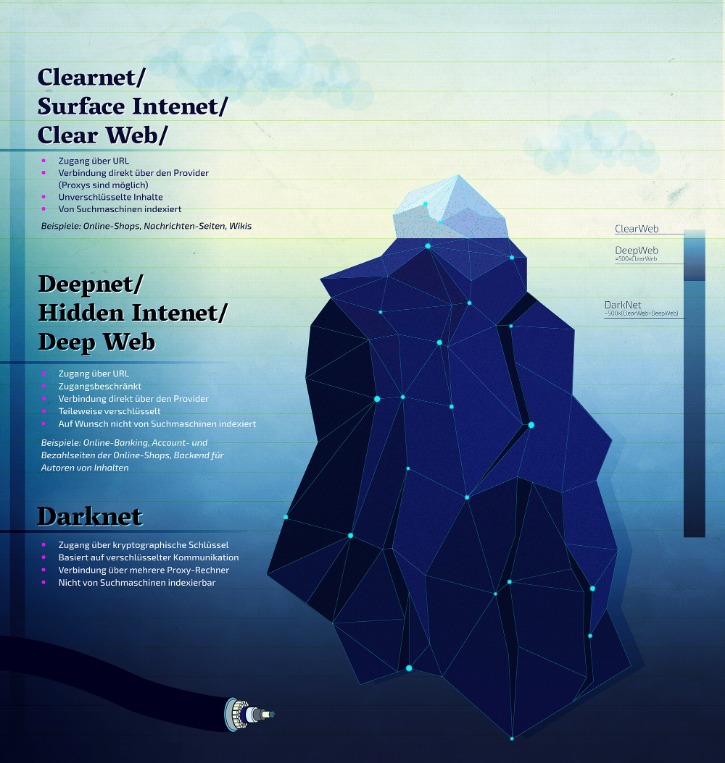
- (b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services.
- The platform is protected from government interference and malicious attacks to protect the user.
- As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
- The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud.
- The files are automatically encrypted, and the sender’s IP is not logged.
How To Avoid Phishing Scams And Malware Threats
Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Through the dark web, users in places of high censorship can also access information and news.
Is It Illegal To Visit Onion Sites?
Now, places like ASAP are talking decentralized setups, spreading the load across nodes so they’re harder to shut down. I’ve seen some beta versions popping up on forums, and they’re rough but promising. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity.
The Legality Of Accessing The Dark Web

Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. However, many are used for illegal activity and onion websites are often popular hangouts for cybercriminals and scammers. Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine. They offer user generated reviews of forums and darknet markets, alongside breaking stories and news from the Tor-sphere. Silk Road was once the most well-known dark web marketplace, but after its shutdown, many new markets took its place.
Perico Market is a newer entrant to the darknet market scene, notable for focusing on strong privacy practices, Monero-only payments, and clean UI. Due to law enforcement, many markets now require invites, referrals, or verified PGP identities. Recent reports indicate Libertas Market is a reputable for fake vendors and very poor customer support with very low buyer confidence. Recent reports indicate Berlusconi Market is a reputable for fake vendors and very poor customer support with very low buyer confidence.