Any use, including reproduction requires our written permission. Stick to tried-and-tested sites and do your best to avoid scams. If you manage to not expose your private information and avoid illicit activities, you can be sure everything will be okay. No one can force you to visit a drug-selling site, give out your info, and buy cocaine or something else.
Does Tor Slow Down My Internet Connection?
- You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom.
- In some countries, exploring new political ideologies can be considered an imprisonable offense, and those who visit restricted websites could be placed on a watchlist or targeted for jail sentences.
- Any website that is paywalled, such as the text of news articles or educational content site that requires a subscription, is also blocked from search engine bots.
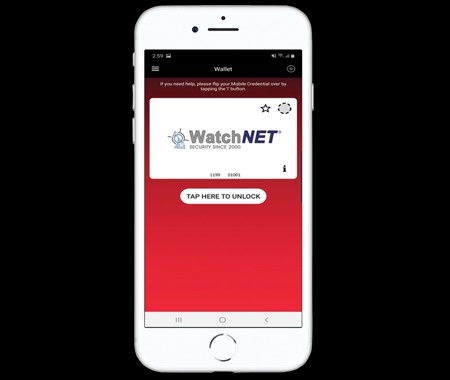
- Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing.
- Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
The Silk Road founder was eventually apprehended and put behind bars for life without the possibility of parole. While similar websites like Silk Road have tried to surface, the government’s double effort on cracking them down has made that unsuccessful for the most part. While operational, the Silk Road was the hub for various illegal transactions. Since the site ran on Tor, which granted a high level of anonymity, users could trade weapons, hard drugs, and other illegal substances. Payments were primarily in bitcoins, further contributing to the site’s safety and security. In darknet mode, you can select friends on the network and only connect and share dark web content with them.

Consider Using A VPN

If the traffic passes through a Tor exit node run by a law enforcement agency, they will only see the IP address that the VPN assigned, not your real IP. As a result, it would be difficult to locate you or trace the dark web activity back to you. No, the dark web isn’t illegal, but what you do while in the underbelly of the internet matters. A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense. There are no laws restricting access to websites on the dark web. However, using the dark web for illegal activity can be a criminal offense.
However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources.
Deep Web Search Engines
When accessing the dark web, the first step is to install a dark web-friendly browser on your computer. Unlike traditional browsers, this will route your internet traffic through an anonymizing network and mask your IP address. Unlike the publicly accessible surface web, the deep web includes sites requiring login credentials but is still accessible via traditional browsers. The dark web is a small, hidden subset of the deep web that requires special tools to access. First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests.
PRIVACY ALERT: Websites You Visit Can Find Out Who You Are
There’s no such thing as perfectly private or secure on the internet. It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult. There are different levels of security in the browser that are worth considering. To review security settings, click on the onion logo in the top left and select “Security Settings”, which will bring up a slider offering a choice of the default of standard, or safer and safest. In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play. Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites.
How To Get On The Dark Web Using Tor Browser
The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites. Dark net websites are called “Tor hidden services”, and they can be distinguished from normal websites by their URLs. Internet providers and websites can detect when Tor is being used because Tor node IPs are public.
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer.
How To Find New, Active Dark Web Links
Although the deep web and the dark web may seem intimidating and dangerous, they’re actually surprisingly simple services to get started with and use. Crawling is the process by which search engines scour the internet for new content and websites. That’s not to say that the entire deep web consists of these difficult-to-find websites. The deep web — also known as the deep net — is a collective term for non-indexed websites that are invisible to traditional search engines. Because of this, tracking down the web addresses of deep web sites is a much more manual process. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites.
Best Practices For Accessing The Dark Web

The real question is—how much of the internet are we not seeing? Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. This information can be used to target ads and monitor your internet usage.
This adds an extra layer of protection to thwart tracking and monitoring in case the traffic passes through a compromised exit node. The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. NordVPN allows you to create your private encrypted network for safe file sharing and work using its Meshnet feature. It uses dedicated IP addresses, enabling you to access IP-restricted networks.
- For example, you could find a passport from a UK citizen there for under a million dollars.
- Often, what you can’t find in a search engine, you can find in various government and open access journals that you can search on Google.
- If you are reading this, you’ve likely heard about how the Tor Browser can help protect your internet privacy and anonymity online.
- It uses TrustedServer technology on the entire server network to wipe out your data after every session.
By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. That way, you can change your passwords and lock down your accounts to help block scammers from using your data against you. While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. Sometimes all you need are credentials like a login or other access privileges.