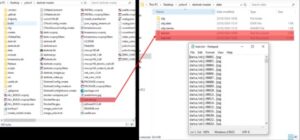
Features like multi-signature wallets, end-to-end encrypted messaging, and decentralized hosting environments reduce the risk of detection. Many vendors rotate addresses and aliases regularly to avoid tracking and maintain anonymity. Operators of these markets implement strict entry barriers, requiring encryption keys and multi-factor authentication.
And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. However, the shift to DeFi illustrates that illicit actors remain highly adaptive and willing to innovate in response to regulatory pressures. The decentralized nature of DeFi platforms complicates compliance and monitoring efforts, challenging enforcement authorities to continuously evolve their tracking and detection methods. In addition, financial institutions and other persons that engage in certain transactions or activities with the sanctioned individual may expose themselves to sanctions or be subject to an enforcement action.
- Bulletproof hosting providers may ignore abuse requests and other legal requests because they are often based in countries that lack strict internet regulations.
- Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps.
- Nevertheless, he was arrested by US officials in December 2022 and charged by the SEC with violating anti-fraud and market manipulation provisions of the securities laws.
- Known for its tight-knit community and high-value listings, Elysium favors privacy-oriented coins like Monero and employs a closed, invite-only system to limit access.
- The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
Implications For Cybersecurity And Data Protection
While this may all sound sophisticated, it is a financial crime and very risky. Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen.

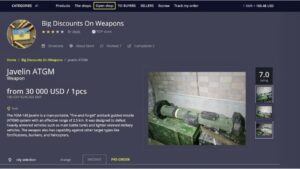
Illicit Payments
The adoption of privacy coins like Monero is increasing due to their non-traceability and lower transaction fees. However, it is essential to note that illicit activity represents only a small fraction of the overall cryptocurrency market. With the increasing adoption of privacy coins like Monero, the dark web has witnessed a shift towards more non-traceable transactions.
Surge In New Scams As Pig Butchering Dominates
As NFTs entered the mainstream, attackers began to target novice NFT investors by exploiting the “FOMO” – fear of missing out – and hype surrounding the NFT world. Deceptive smart contracts are intentionally designed to trick users into transferring funds or granting permissions to them. The most notable example of this is drainware – smart contracts that, upon interaction, grant the attacker permission to move funds from the victim’s wallet. The past few years have witnessed a rise in the attempted use of cryptocurrency to pay for contract killings. It should be noted that there have been no publicly documented examples of a completed murder-for-hire scheme paid for in cryptocurrency at the time of publication.

It also fosters trust, as transactions are verified through the blockchain technology, ensuring that payments are made and received securely. The anonymity provided by cryptocurrency is particularly appealing to dark web users, as it helps to protect their identities and evade detection by law enforcement agencies. Monetary gains have always been the goal for criminals; thus, money laundering is an indispensable component of criminal schemes aimed at concealing the proceeds of illicit acts. The combined anonymity provided by the dark web and cryptocurrencies has proven to be a potent tool in the hands of threat actors, that facilitates the laundering of the gains from their ilicit activities. Since its inception, cryptocurrencies have become the preferred currency for criminals operating on the dark web.
On the dark web, Bitcoin is often used for purchasing a wide range of illegal goods and services. While drugs, including cannabis, cocaine, and MDMA, are the most prevalent items bought with cryptocurrency, there is also a market for stolen credit card data, hacking tools, and counterfeit identities. However, it is important to note that this illegal activity represents only a small fraction of the overall cryptocurrency market.
Niche Trends And Ecosystem Shifts
Fraudulent ICOs, rug pulls, and phishing attacks deceive users through false promotions and impersonation tactics. These threats highlight the need for stronger security measures, regulatory oversight, and increasing user awareness. Cryptocurrency fraud has seen a significant rise in recent years, with various schemes exploiting the digital nature of cryptocurrencies. This section explores Ponzi and pyramid schemes, ICO scams, rug pulls, and phishing attacks, as well as cryptojacking, fake wallets, and fraudulent exchanges.
Torrez Market
In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Our team of highly skilled cybersecurity experts offers advanced solutions designed to counter even the most sophisticated cyber threats. With a strong focus on proactive strategies and forward-thinking approaches, we enable organizations to operate confidently in a secure and threat-free environment.
There’s also a search bar that you can use to search for any particular product or vendor. World Market is another largest dark web shops that deals with various goods and services. Its impressive anti-DDoS protection feature and easy-to-use interface make this marketplace stand out among the others. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. Fifth, we consider the lifetime of each entity i at time t, defined as the time interval between the first and the last transaction performed by the entity until time t, denoted by \(\ell _i(t)\). This feature is satisfied when \(\ell _i(t) \ge L\), where L is the fixed value of minimum lifetime.
The Top 7 Dark Web Marketplaces In 2025
It allows access to the .onion sites on the dark web that you won’t find using a regular browser. The largest component of the S2S network one year before and one year after the operation Bayonet. Nodes are sellers that are active within the time period, and an edge is placed between two sellers if at least one transaction occurs between them during the period. This suggests that the multiseller activity is sensitive to external shocks but also that it yields higher profits. Cryptocurrencies are digital or virtual currencies that use cryptography for security and operate independently of a central bank. This level of security is particularly appealing to those operating on the dark web, as it provides a level of protection for their illicit activities.
Shuttered Dark Web Marketplaces
The ability to understand and counteract its growth will define the future of cybersecurity and digital law enforcement. Without a single point of failure, decentralized markets prove far more difficult to shut down. Law enforcement cannot trace server IPs or arrest administrators because the markets have none. These systems use cryptographic access credentials, distributed file storage, and token-based payments to build fully autonomous criminal economies.
Illicit Crypto

While cryptocurrencies offer a level of anonymity and privacy that is attractive to those operating on the dark web, they also present several risks and challenges that must be addressed. As law enforcement agencies continue to develop new tools and technologies to combat cryptocurrency use on the dark web, it is likely that we will see increased regulation and oversight of cryptocurrency transactions. They are distinct from independent single-vendor shops that also sell illicit drugs, and from other types of fraud stores.As much as USD 1.49 billion was spent on DNMs in 2022, according to TRM Labs research. By contrast, the largest Western Bitcoin DNM currently in existence – ASAP Market – accounted for less than 10% of global DNM market share. Most Russian-language DNMs only support Bitcoin, with no privacy coin options available.
Darknet Vendors Shift To DeFi As Crypto Laundering Tactics Evolve
However, after the operation Bayonet, although the network shows a decrease in connectivity, it still remains highly connected and with a large number of active multibuyers. Moreover, the network had already fully recovered by 2019 showing a strong resilience against external shocks. The empty point on the multiseller median income line demarcates the quarter with only two multisellers. After that quarter, their number remains small, which is represented by the dashed line. The number of sellers in each category and multisellers as a function of time is shown in Fig.