By pooling their efforts, law enforcement and private organizations can stay one step ahead of cybercriminals, ensuring a safer digital environment for everyone involved. Together, we can create a united front against the darknet threat landscape. To protect yourself and your organization from cyber threats, it’s important to follow cybersecurity best practices.
As law enforcement agencies crack down on illegal activities within these markets, vendors are finding innovative ways to evade detection. They employ encryption techniques, utilize decentralized platforms, and explore alternative payment methods to ensure their operations remain covert. This constant cat-and-mouse game between criminals and law enforcement fuels an ongoing evolution in the darknet marketplace ecosystem. Darknet marketplaces are online platforms on the dark web that facilitate the buying and selling of various illegal goods and services, including drugs, firearms, stolen data, and malware. These marketplaces operate on encrypted networks and are designed to conceal the identities of both buyers and sellers through anonymity tools like Tor. The goods on sale range from stolen credit card data and forged documents to illegal drugs, weapons, malware as a service, and hacking tools.
Run Antivirus/Anti-Malware Software
- Please note that our Terms and Conditions, Privacy Policy, and Disclaimers have been updated.
- A VPN encrypts the data traffic and keeps your activities private on the dark web.
- In 2024, it recorded on-chain revenue of $43.3 million, a 183 per cent increase, driven by vendor migrations post-shutdown of competitors, according to Chainalysis’ 2023 market report Darknet revenue in 2023.
- Strict user verification processes aim to filter out potential scammers and law enforcement infiltrators.
By giving malicious actors direct access to sensitive records, these data-focused marketplaces significantly expand the scope and impact of identity-based crimes. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve.
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Reviews are what most DNMs rely on to ensure that they are receiving the products that they are buying. But as demonstrated below vendors will try to explain why they have received bad reviews.
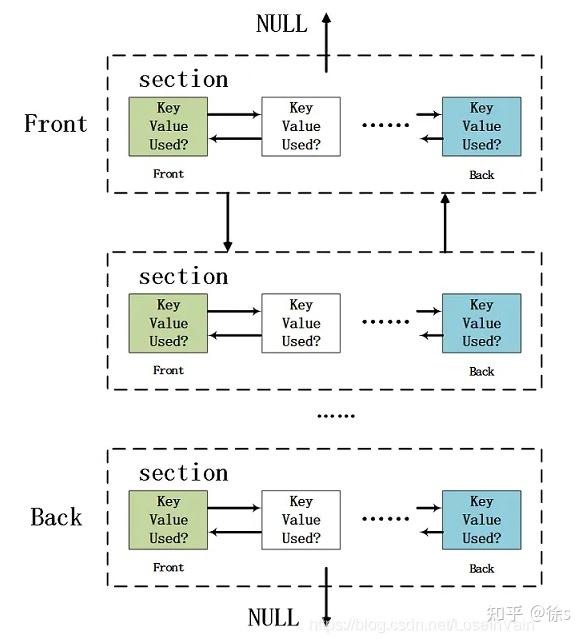
Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails. Going forward, these trends—enhanced anonymity, specialized marketplaces, and increasingly sophisticated fraud—are likely to define the dark web’s trajectory. Cybersecurity professionals and investigators will need to employ equally advanced tools and collaborative strategies to keep pace with the rapidly shifting landscape.
Payment Methods Overview
Listings often include malware kits, exploit software, and zero-day vulnerabilities. Along with these, it hosts sections for counterfeit currency and stolen financial data. Buyers appreciate its support for multiple privacy-focused cryptocurrencies and its layered authentication processes designed to fend off law enforcement infiltration. Complicating matters further is the widening use of alternative channels, such as Telegram groups, private forums, and even hidden social media communities. While .onion services remain central to Dark Web commerce, these additional platforms give cybercriminals greater flexibility and resilience. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities.
Crime Forums And Markets Specializing In Cybercrime Enablement
Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more. Around 300 officers were deployed to carry out enforcement actions and secure critical evidence. Once you have found a vendor you would like to deal with it’s time to do some extra homework on them. For starters, you can put their name into the dread search box, and see if you can find any reviews about them. If everything seems to check out go on a market they vend on and check recent feedback.
Darknet Market Links ( Official )
One of the more intriguing developments in Tor usage is Germany surpassing the United States in user numbers for the first time. Analysts speculate that this shift may be tied to growing privacy concerns in Europe, alongside a broader cultural acceptance of encrypted communication tools. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely.
Is The Dark Web Illegal? Here’s What Not To Do
Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
Darknet Marketplaces Around The World
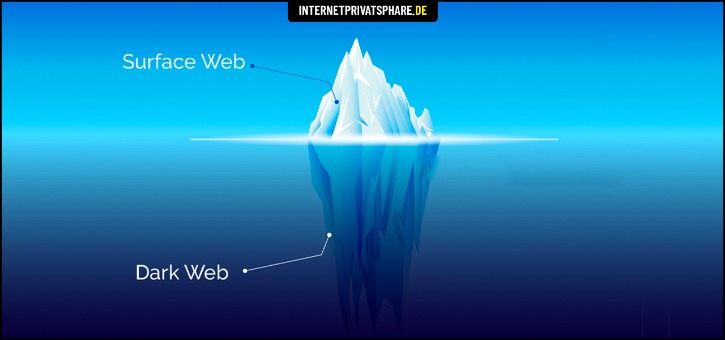
Abacus’s exit follows the June 16, 2025 law enforcement seizure of Archetyp Market, marking the latest in a series of shutdowns in the Western DNM ecosystem. KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. The two most popular product categories are counterfeit currency follower by counterfeit IDs.

The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce.
Shaping The Future Of Torzon Darknet
Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.
Other Government Sites
Stolen credit card numbers, bank login credentials, and identity documents are consistently in high demand. Buyers often use these details for fraudulent purchases or large-scale identity theft schemes. With global e-commerce on the rise, criminals capitalize on weaker security protocols in certain regions, transforming credit cards and personal data into high-value commodities. The ease of encryption-based communication and anonymous digital payments helps keep transactions hidden from regulators and financial institutions, perpetuating the cycle of fraud and data theft. This operation led by the German authorities marks the end of a criminal service that enabled the anonymous trade in high volumes of illicit drugs, including cocaine, MDMA, amphetamines, and synthetic opioids.