Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. Although the deep web and the dark web may seem intimidating and dangerous, they’re actually surprisingly simple services to get started with and use. Many use the technology to engage in illicit activities, but there are many legitimate reasons for accessing the deep net, especially in countries with poor digital privacy laws such as the United States. The Silk Road was a marketplace on the dark web that launched in 2011, where you could purchase all sorts of illegal goods.
How To Access The Dark Web
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.

The vast majority of transactions consisted of illegal drugs, but you could also find weapons, personal information, child pornography and stolen credit card details. Allegedly, it was also possible to hire hit men on the site, though it’s never been proven that any of these contracts were actually fulfilled. Tor encrypts your traffic through multiple relay nodes, but it’s important to understand that this encryption is removed at the exit node before reaching its final destination. This means that if you’re accessing non-HTTPS websites, the exit node operator could potentially view your unencrypted traffic. Here’s a guide that will help you learn about the dark web, the sites that populate it, and how you can visit it safely using the added protection of a VPN and antivirus software. By using Tor over VPN, the VPN encrypts your data and hides your IP address.
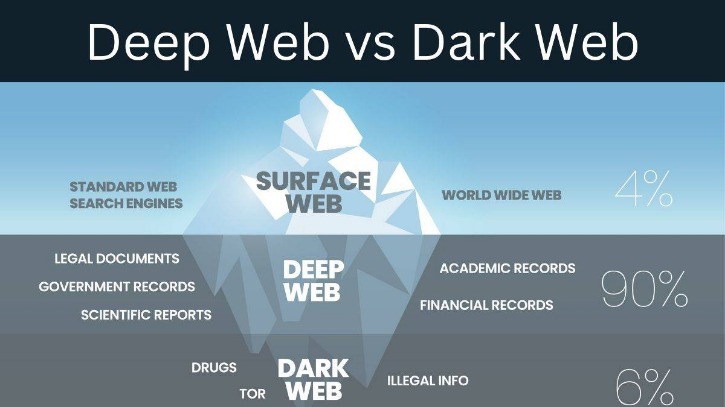
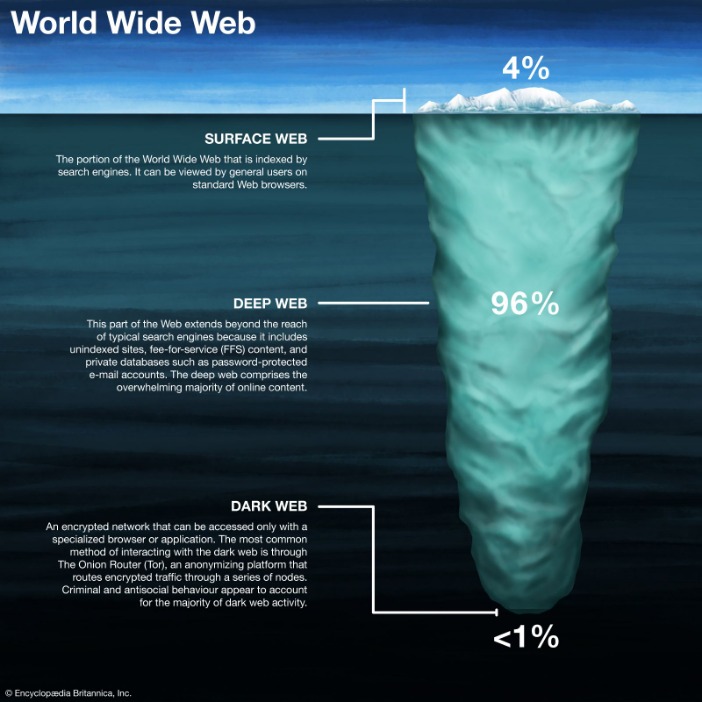
Surface Web Vs Deep Web Vs Dark Web Vs Darknet
That’s why forward-thinking buyers are securing Deep Sky Tonnes today. Deep Sky builds, owns, and operates the infrastructure to reverse climate change. We help you remove emissions with the highest-quality carbon removal credits on the market. We’re a nonprofit organization and rely on supporters like you to help us keep Tor robust and secure for millions of people worldwide.
Is Tor Illegal To Use?
You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you.
- It allows you to search for images, maps, files, videos, social media posts, and more.
- As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
- And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.
- It hosts both legal and illegal activities, offering anonymity but also posing risks like scams and illicit content.
OnionName — Buy Readable Onion Domains
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
Remember, knowledge is power, but with power comes responsibility. One of the golden rules of navigating the Deep Web safely is to refrain from sharing personal information. This includes not using your real name, email address, or any identifiable details when registering or participating in discussions. By maintaining a high level of anonymity, you can safeguard your online identity effectively. Websites on the Deep Web often use encryption protocols such as HTTPS to secure the data transferred between the user and the server. This ensures that your sensitive information remains confidential and protected from prying eyes.
Download The Tor Browser
To secure the next 150 years for humanity, Deep Sky aims to remove gigatons of carbon from the atmosphere and permanently store it underground, back where it belongs. The Thetford Mines community welcomed Deep Sky, recognizing its sequestration project as an opportunity for job creation and economic development. Their support is essential to building a sustainable carbon removal hub in the region. Deep Sky creates jobs, boosts local economies, and supports sustainable industries.
Safely Accessing The Deep Web And Dark Web
Some of these are well-known, established threats that circulate in this nook of the web. However, others may be taking advantage of the dark web’s reputation to trick users out of large sums of money. Also, some users on the dark web may attempt phishing scams to steal your identity or personal information for extortion. The threats of online browsing can extend into the unplugged world if your computer or network connection can be exploited. Anonymity is powerful with Tor and the framework of the dark web, but it is not infallible.
David Fraser, a partner at Halifax law firm McInnes Cooper and noted privacy expert, says, generally speaking, police are free to peruse the internet and take note of what they find. He adds that the RCMP, which has been funding the research with the eye to eventually buy the software, has different objectives. In 2014, Frank developed a web-crawling program that can tag and track images of child pornography.
Securely Offline Yourself From Dark Web

Investigators in Calgary say police crackdowns haven’t been enough to suppress the growing appeal of dark web markets. But the dark web also offers drug traffickers cover from police surveillance. “Given that the dark web is anonymous, it allows for a very easy vehicle in order for people to buy drugs,” Lalande says. In a recent scan of the site, Dream featured roughly 1,000 listings for drugs that ship within Canada, ranging from opium, morphine and fentanyl to ecstasy, ketamine and date-rape drugs. Liam buys only from Canadian drug vendors, fearing that importing heroin and meth across the border would put him at risk of investigation by the Canada Border Services Agency. The CBSA has the authority to open and inspect any package entering the country.
It operates in both French and English and has built a reputation for ease-of-use. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. This article reveals the top 10 dark web markets dominating in 2025, their unique characteristics, and the critical implications for enterprise cybersecurity. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. To expand their reach, some marketplaces established parallel channels on Telegram.
Hidden Answers
The algorithm is said to be updated regularly, and the user interface is very straightforward, so if you are looking for an entry point into the Deep Web, this is a good place to start. Live OS options that can be run on nearly any computer by simply popping a USB stick in and booting from it include Subgraph OS, Freepto, and Tails. Yes, Tor-capable browsers are available for both major mobile platforms, Android and iOS. Now you have enough information about what Tor is, how it works, and how best to use it, allowing you to make an informed choice on its proper use, and how to best protect yourself online when using it. The dark web is a refuge for information leakers and whistleblowers.
Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cards, fake passports, malware kits, untraceable drugs, anything. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results.



