In some authoritarian states, accessing Tor nodes can flag you for surveillance. This article aims to clarify these concepts, explore their differences, and highlight their respective purposes and risks. These hidden networks intentionally conceal IP addresses and encrypt communications through multiple layers of routing. Understanding the relationship between Tor and the dark web is essential—Tor (The Onion Router) is the primary software used to access these hidden sites.
If your password or other credentials are the key to unlocking this data, then cybercriminals will attempt to steal these credentials via phishing, social engineering, malware, and other means. The risks of accessing the Dark Web include exposure to illegal content, potential scams, malware, and legal repercussions if one inadvertently engages in illicit activities. It includes legitimate resources such as academic databases and private networks, as long as users respect privacy laws and do not engage in unauthorized activities. The dark web is a subset of the deep web that requires special software, like the Tor browser, to access. Known for its focus on anonymity, the dark web is often linked to illegal activities, although it also serves as a platform for privacy advocates and journalists in repressive regimes. There are also discussion forums, hacking communities, and message boards focused on topics ranging from cybersecurity and cryptography to more disturbing and illegal content.
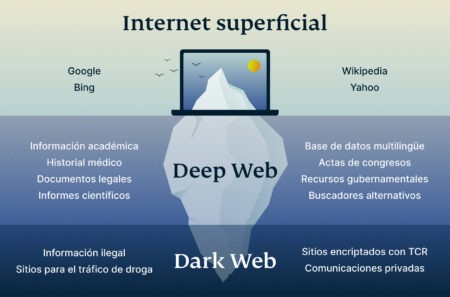
Most internet users browse content online using the surface web, a segment of the internet where sites are indexed by popular search engines and can be easily viewed using traditional web browsers. While the surface web may represent most of what the average user sees, there are many more layers of hidden content to be found on the dark web. Using a special browser known as The Onion Router (Tor), users can explore these hidden sites and engage in both legal and illicit activities under the cover of an anonymous IP address. Here’s a look at how the dark web works and the many ways in which people use it, both legally and illegally. The deep web vs dark web are often misconstrued as being one thing when in reality they represent two different levels of the internet. The deep web refers to all that is accessible on the internet that is not indexed with those typical search engines.
Data Link Layer

As for the dark web, it’s intentionally hidden, encrypted, and made anonymous. As you can probably imagine, that’s exactly what threat actors on the internet want to hide their nefarious deeds. We can’t discuss the history of the dark web without understanding the history of TOR, the most popular dark web network. The principle of ‘onion routing’, which underpins TOR, was developed by the researchers Paul Syverson, Michael G. Reed and David Goldschlag at the United States Naval Research Laboratory in the 1990’s.
The threats of online browsing can extend into the unplugged world if your computer or network connection can be exploited. Anonymity is powerful with Tor and the framework of the dark web, but it is not infallible. Any online activity can carry breadcrumbs to your identity if someone digs far enough. The dark web was once the province of hackers, law enforcement officers, and cybercriminals. However, new technology like encryption and the anonymization browser software, Tor, now makes it possible for anyone to dive dark if they’re interested. The dark web has numerous legitimate uses but is still home to various criminal activities.
With only about 4 percent of all online content freely accessible (making up the surface web), the remainder is tucked away in the deep web. This means there is no easy, direct way for the general public to search this vast amount of unindexed content. In some cases, websites use various methods to block spiders and prevent indexing. These methods include using CAPTCHAs, multiple IP addresses for the same content, non-HTML content or data that spiders cannot pick up, password protection, and unlinked content. The dark web is also legal to access, but it comes with serious risks.
Exposure To Harmful And Illegal Activities

Content remains invisible to search engines, requiring users to possess specific credentials or URLs. Most deep web resources serve legitimate purposes and exist to protect confidential information rather than conceal illegal activities. It requires specific software and knowledge to access, creating a barrier that keeps casual internet users away. Unlike standard websites, dark web sites use encryption technologies like The Onion Router (Tor) to mask user identity and activity.
A Quick Guide On How To Use A VPN With Tor
Besides the illegal activities on the Dark Web, political dissidents and privacy advocates also use it for anonymity. Well-known organizations like Facebook and DuckDuckGo have Web sites on the Dark Web. It’s not as convenient as the Surface Web, but anyone of average technical prowess can use it. The concept known today as the Dark Web set its foundation in the early 2000s. In March of 2000, Freenet was released to allow a censorship-resistant way to use the Web.
Top VPN Deals

So, the very first thing you need when you wish to access the deep/dark web is URLs. And because dark web URLs are .onion and because they’re pretty long, and consist of random numbers and alphabets, you can’t exactly memorize them. Once you get a VPN, it not only hides your real IP address, but also encrypts your internet traffic and protects you from hackers and snoopers. A VPN is a “Virtual Private Network”, it may sound complicated but it’s just a software which hides your actual IP address, and assigns you a secondary IP which can’t be linked back to you.
- Still, even if it were real or will be real, paying for access is not the way to go.
- Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.
- Most dark websites are used for illegal and illicit activity, but a few legal sites exist.
- Despite all the dangers, there are actually advantages to using the dark web.
- However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes.
- It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers.
Use A Secondary Non-admin Account
The deep web refers to non-indexed webpages as a whole, while dark web refers more specifically to the parts of the deep web where you can engage in illicit activities. Aleksander Hougen, the co-chief editor at Cloudwards, is a seasoned expert in cloud storage, digital security and VPNs, with an educational background in software engineering. Beyond his prolific writing commitment, Aleksander helps with managing the website, keeping it running smoothly at all times. He also leads the video production team and helps craft e-courses on online technology topics. Outside of the professional realm, he is a digital nomad with a passion for traveling, having lived in many countries across four continents.
HTML Attachments: A Gateway For Malware?

Criminals use it to buy and sell stolen data, commit identity theft, or conduct illicit transactions. On the other hand, accessing the dark web requires special software, most commonly Tor, which masks your identity and provides access to websites with .onion extensions. Surface web search engines do not index these sites, so you need the right tools to navigate safely and anonymously. In the deep net, web crawlers are blocked from accessing web pages to gather information for indexing, so the content remains hidden. Some content and services on the deep web are indexed by search engines, but paywalls or password protection prevent access.
- As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously.
- It even has a dark web monitor to notify you in case your data gets leaked on the dark web.
- Law enforcement routinely shuts down and prosecutes sites and people doing illegal things on the Dark Web.
- One option is to try DuckDuckGo’s .onion version, which is great for privacy.
- Tor has an in-build slider which lets you adjust the level of security.
- These websites exist in directories that Google (and other search engines) are barred from crawling.
When you log in to your favorite video streaming site or check your bank account balance online, that’s the deep web at work. Yes, police can track users on the dark web, but it’s challenging and resource-intensive, requiring advanced tools, undercover operations, and digital forensics to uncover illegal activity. So, while the dark web is designed for anonymity, it’s not impenetrable — mistakes by users, metadata leaks, compromised devices, or cooperation from hosting providers can all lead to exposure. What is illegal is not just to access and browse the overlay networks called the deep web or dark web, but to look into illegal services sold on these networks. That’s what can get someone in trouble, not just simply the browsing.
Understanding BlackCat Ransomware: Threat Overview And Protective Measures
While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
How To Access The Dark Web
People might operate under anonymity without revealing their identity, which could protect their privacy but can also lead to illegal activities. Using dark web browsers like Tor is legal in most countries, but accessing illegal content or services remains unlawful regardless of the technology used. Organizations should establish clear policies governing the acceptable use of anonymizing technologies by employees. Unlike the dark web, which requires specialized browsers, deep web content often exists on the regular internet but remains inaccessible without proper authentication or direct links. As previously mentioned, more than 90% of the traffic on the internet is already on the deep web, so the keys to accessing it safely are virtually the same as the keys to accessing the open web safely. Though you don’t have to perform a penetration test on every website you log in to, you should ensure that it runs on a secure framework that uses HTTPS encryption.
The report reveals that in 2024, over 100 billion stolen credential records were shared in underground forums, a 42% increase from 2023. According to Fortinet’s 2025 Global Threat Landscape Report, the darknet has evolved from a mere refuge for cybercriminals into a supply chain for cyberattacks. In the CrowdStrike 2024 Threat Hunting Report, CrowdStrike unveils the latest tactics of 245+ modern adversaries and shows how these adversaries continue to evolve and emulate legitimate user behavior.



